Global Attack Surface Management Market Size, Share and Analysis By Component (Solutions, Services), By Deployment (Cloud, On-premise), By Enterprise Size (SMEs, Large Enterprises), By End Use (BFSI, Healthcare & Life Sciences, Retail & E-commerce, IT & Telecommunications, Government & Public Sector, Manufacturing, Energy & Utilities, Others) , By Regional Analysis, Global Trends and Opportunity, Future Outlook By 2025-2035
- Published date: March 2026
- Report ID: 182517
- Number of Pages: 381
- Format:
-
keyboard_arrow_up
Quick Navigation
Report Overview
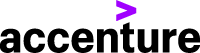
The Global Attack Surface Management Market size is expected to be worth around USD 45.67 billion by 2035, from USD 2.34 billion in 2025, growing at a CAGR of 34.6% during the forecast period from 2025 to 2035. North America held a dominant market position, capturing more than a 36.4% share, holding USD 0.85 billion in revenue.
Attack Surface Management (ASM) market refers to the ecosystem of solutions and services designed to continuously identify, monitor, and mitigate vulnerabilities across an organization’s digital, physical, and human assets. An attack surface includes all possible entry points such as applications, cloud systems, networks, and connected devices that can be exploited by attackers. ASM platforms provide real time visibility, asset discovery, and risk prioritization, enabling organizations to secure both known and unknown assets.
Top driving factors of this market are strongly linked to the rapid expansion of digital infrastructure and the rising frequency of cyber threats. Organizations are adopting cloud computing, remote work models, and IoT ecosystems, which significantly increase the number of potential entry points for cyberattacks. Cybercrime costs are projected to exceed $10 trillion annually, highlighting the urgency for proactive security strategies.
Additionally, the average cost of a data breach has reached over $4 million, pushing enterprises to invest in preventive security frameworks such as ASM. Demand analysis indicates that enterprises are increasingly shifting from reactive security models to proactive risk management approaches. A notable transition is observed where organizations are implementing continuous monitoring rather than periodic assessments.
It is estimated that around 60% of organizations are expected to formalize ASM programs within a few years, compared to less than 10% adoption earlier, reflecting a sharp rise in enterprise awareness and urgency. Demand is particularly strong in sectors handling sensitive data such as finance, healthcare, and digital services
For instance, in October 2025, Qualys enhanced its ASM solution with AI-powered prioritization, reducing alert fatigue by 70%. The platform now correlates vulnerabilities across cloud, endpoints, and networks automatically. Security teams using the update closed critical exposures 3 weeks faster than industry benchmarks.
Key Takeaway
- The Solutions segment accounted for a leading 70.3% share, indicating strong reliance on integrated security platforms.
- Cloud-based deployment dominated with a 58.9% share, reflecting the shift toward scalable and remote security infrastructure.
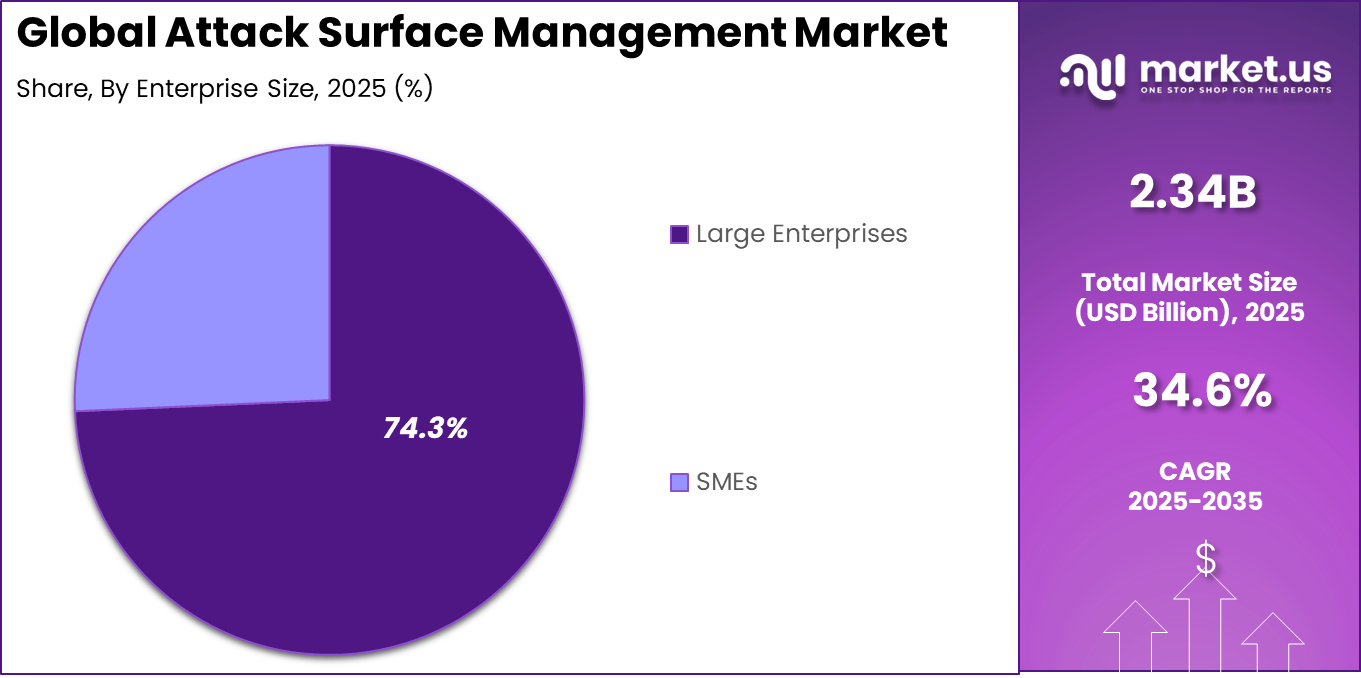
- Large enterprises contributed the highest adoption, holding a 74.3% share due to complex and expanding digital environments.
- The BFSI sector emerged as a key end user, capturing 36.6% share driven by high sensitivity to cyber risks.
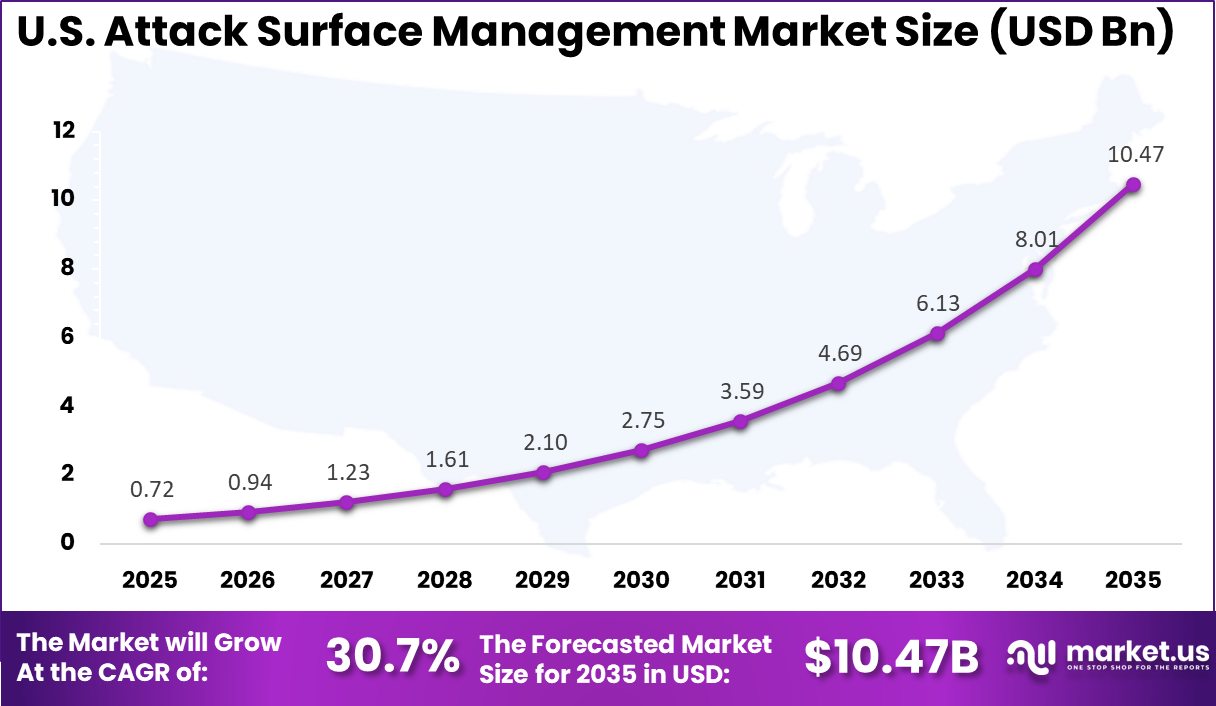
- The U.S. market was valued at USD 0.72 billion in 2025, supported by a strong 30.7% growth rate.
- North America led regionally with over 36.4% share, supported by advanced cybersecurity investments and infrastructure.
Component Analysis
In 2025, The Solutions segment held a dominant market position, capturing a 70.3% share of the Global Attack Surface Management Market. This dominance is due to the need for centralized visibility and control over expanding digital assets. Organizations prefer solutions that combine asset discovery, vulnerability detection, and risk prioritization in one place. These tools simplify complex security operations and support continuous monitoring, helping teams manage risks more efficiently across dynamic environments.
Solutions also reduce reliance on manual processes by automating the identification and assessment of exposed assets. This improves response time and accuracy in threat management. As cyber risks grow more complex, businesses increasingly adopt solution based approaches to maintain consistent protection and strengthen their overall security posture.
For Instance, in January 2026, Tenable launched smarter scanning features that prioritize real-world risks over noise. Users report quicker fixes for vulnerable endpoints, easing the load on stretched IT crews. By blending exposure data with threat intel, it strengthens defenses without overwhelming staff. Companies see it as a game-changer for staying proactive.
Deployment Analysis
In 2025, the Cloud segment held a dominant market position, capturing a 58.9% share of the Global Attack Surface Management Market. This dominance is due to the growing shift toward cloud based infrastructure across industries. Businesses require flexible systems that can adapt to constantly changing digital environments. Cloud deployment allows faster implementation and seamless monitoring of distributed assets, making it easier for teams to maintain visibility across remote and hybrid setups.
Cloud based platforms also support real time updates and remote accessibility, which improves operational efficiency. Security teams benefit from scalable resources that adjust to workload demands. As organizations continue digital transformation, cloud deployment becomes a practical choice for maintaining continuous and reliable attack surface monitoring.
For instance, in February 2026, Microsoft enhanced its cloud security platform with seamless attack surface mapping for Azure users. It spots exposures in dynamic setups, letting admins scale protection effortlessly. This update supports remote teams tracking assets on the fly, reducing gaps in fast-moving cloud environments. Feedback highlights its role in simplifying hybrid shifts.
Enterprise Size Analysis
In 2025, The Large Enterprises segment held a dominant market position, capturing a 74.3% share of the Global Attack Surface Management Market. This dominance is due to the complexity of large enterprise IT environments, which include multiple networks, applications, and endpoints. These organizations face higher exposure to cyber risks, requiring advanced tools to monitor and manage their attack surface. Strong focus on data protection and compliance further drives adoption of comprehensive security systems.
Large enterprises also have greater financial capacity to invest in advanced technologies and skilled teams. This allows them to implement robust monitoring strategies and maintain continuous oversight of vulnerabilities. Their scale and operational diversity make structured attack surface management essential for reducing risks and ensuring business continuity.
For Instance, in January 2026, IBM unveiled enterprise tools for mapping vast global infrastructures, tackling shadow IT head-on. Large ops gain end-to-end visibility, vital for complex chains. It streamlines audits and compliance checks across borders. Big firms find it scales well, turning big risks into managed routines.
End Use Analysis
In 2025, The BFSI segment held a dominant market position, capturing a 36.6% share of the Global Attack Surface Management Market. This dominance is due to the critical nature of financial data handled by banks and institutions. These organizations are frequent targets of cyber threats, making continuous monitoring a priority. Strong regulatory requirements also push them to adopt advanced tools that help identify vulnerabilities and maintain strict security standards.
The BFSI sector also focuses on protecting customer trust and preventing financial losses. Attack surface management supports early detection of risks across digital channels such as online banking and payment systems. This enables institutions to strengthen defenses and maintain stable and secure financial operations in a digital environment.
For Instance, in February 2026, CyberArk strengthened identity protections for financial networks, exposing weak privilege points. Banks use it to secure APIs and vendor links under heavy scrutiny. It cuts insider and external risks tied to transactions. BFSI pros note its fit for regulatory demands, building trust through solid safeguards.
Regional Analysis
In 2025, North America maintained its dominant position in the Attack Surface Management market, capturing a 36.4% market share. The region’s strong cybersecurity infrastructure and technological advancements have contributed to its leadership role.
For instance, in February 2026, CrowdStrike Falcon Surface platform expanded with new third-party exposure monitoring, giving U.S. enterprises unprecedented visibility into supply chain vulnerabilities. The Texas-based firm’s real-time threat intelligence reinforces North America’s ASM supremacy as cyber threats grow more sophisticated daily.
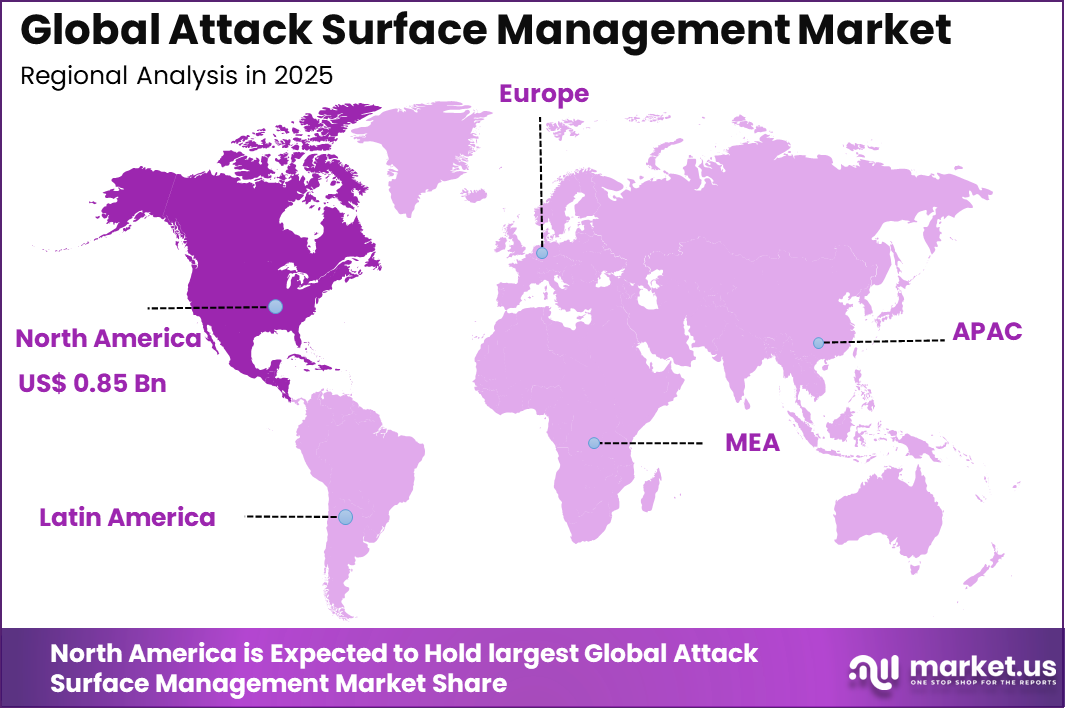
The U.S. alone accounted for USD 0.72 billion in market value, with a projected CAGR of 30.7%. North America has been proactive in adopting cutting-edge cybersecurity solutions across various industries. The increasing number of cyberattacks and the adoption of digital transformation strategies have heightened the demand for solutions that provide robust protection.
The U.S. is a key player in the development and implementation of Attack Surface Management solutions, driven by the need for comprehensive security measures in sectors such as BFSI, healthcare, and government. As businesses in North America continue to adopt advanced technologies, the demand for security solutions that can protect these digital assets will remain high.
For instance, in March 2026, Cisco strengthened U.S. dominance in Attack Surface Management by launching SecureX 2.0, integrating AI-driven asset discovery across cloud and on-premises environments. This innovation helps enterprises continuously monitor and reduce their digital attack surface, solidifying Cisco’s leadership from its California headquarters.
Emerging Trend Analysis
A key emerging trend within the attack surface management market is the shift towards proactive security practices that provide continuous monitoring of digital assets. As organizations expand their digital footprints across various platforms, including cloud, on-premises, and IoT devices, the need for real-time asset discovery and ongoing vulnerability assessment becomes essential.
This evolution from reactive to proactive security is driven by the growing complexity of IT environments, which require constant vigilance to identify potential vulnerabilities before they are exploited by cyber threats. Continuous monitoring allows security teams to detect unknown assets, assess risks in real-time, and respond to emerging threats more effectively.
In response to these demands, modern attack surface management tools are evolving to integrate advanced technologies such as machine learning and predictive analytics. These solutions offer automated alerts, prioritization of vulnerabilities, and real-time threat intelligence, enabling organizations to stay ahead of cybercriminals. This proactive approach helps businesses mitigate risks, reduce response times, and enhance overall security resilience, positioning attack surface management as a critical element in modern cybersecurity strategies.
Key Market Segments
By Component
- Solutions
- Services
By Deployment
- Cloud
- On-premise
By Enterprise Size
- Large Enterprises
- SMEs
By End Use
- BFSI
- Healthcare & Life Sciences
- Retail & E-commerce
- IT & Telecommunications
- Government & Public Sector
- Manufacturing
- Energy & Utilities
- Others
Key Regions and Countries
North America
- US
- Canada
Europe
- Germany
- France
- The UK
- Spain
- Italy
- Russia
- Netherlands
- Rest of Europe
Asia Pacific
- China
- Japan
- South Korea
- India
- Australia
- Singapore
- Thailand
- Vietnam
- Rest of APAC
Latin America
- Brazil
- Mexico
- Rest of Latin America
Middle East & Africa
- South Africa
- Saudi Arabia
- UAE
- Rest of MEA
Drivers
Escalation of Cybersecurity Threats
One of the key drivers of the attack surface management market is the escalating number and sophistication of cybersecurity threats. As organizations move more operations online, they expose themselves to a larger attack surface, attracting the attention of increasingly advanced cybercriminals. This growth in digital threats, including ransomware and data breaches, has prompted businesses to adopt solutions that provide deeper visibility into their digital assets and the vulnerabilities they may contain.
The growing frequency of attacks has heightened the awareness of cybersecurity risks among business leaders, driving investment in solutions like attack surface management. By gaining continuous insight into their exposed assets, organizations can take a more proactive stance against emerging threats. As the complexity of cyberattacks increases, so does the demand for effective ASM tools that can identify weaknesses and ensure better protection of digital environments.
For instance, in March 2026, Cisco rolled out updates to its secure cloud tools, spotlighting how more online assets draw hacker attention amid rising remote work setups. Teams now get clearer views of exposed spots, helping them act fast on threats that slip through cracks from expanded digital footprints. This move underscores the push to guard against everyday vulnerabilities that attackers probe daily.
Restraint
High Implementation and Operational Costs
A significant barrier to the widespread adoption of attack surface management solutions is the high cost of implementation and maintenance. Many organizations, particularly smaller businesses, find the upfront investment required for deploying these tools prohibitive. The costs of acquiring software, integrating it with existing systems, and training personnel to effectively manage it can be substantial.
These financial burdens can deter some companies from adopting ASM solutions, even as the need for them grows. Additionally, maintaining ASM tools can be resource-intensive. The continuous monitoring and analysis of data generated by these tools requires skilled professionals who can interpret alerts and take appropriate action.
The complexity of managing large datasets and responding to potential threats in real-time can strain internal resources, increasing operational costs. As a result, smaller organizations with limited budgets may struggle to fully leverage the benefits of attack surface management.
For instance, in December 2025, Qualys discussed challenges in scaling their vulnerability management across tangled networks, where setup demands custom tweaks for diverse assets. Overloaded staff grapples with configuration puzzles that disrupt workflows, making broad adoption tougher than expected. It captures the real friction in turning promising tech into daily practice.
Opportunities
Integration with Cloud Security Solutions
The growing adoption of cloud technologies presents a significant opportunity for attack surface management tools to evolve and integrate more deeply with cloud-native security solutions. As businesses increasingly move to cloud environments, ensuring the security of digital assets becomes more complex.
Attack surface management tools that integrate seamlessly with cloud platforms offer businesses enhanced visibility and control over their assets, regardless of where they are located. By aligning ASM solutions with cloud-native security features such as identity management and automated threat detection, organizations can better secure their digital infrastructures.
The opportunity to integrate ASM into cloud environments not only enhances security but also simplifies the management of digital assets. As cloud computing continues to grow, the demand for integrated ASM solutions that provide automated risk assessment and vulnerability management will increase, offering organizations a streamlined approach to cybersecurity.
For instance, in November 2025, Palo Alto Networks previewed AI features in their next-gen security ops, aimed at real-time risk mapping across sprawling environments. Automating anomaly detection cuts manual work and spots hidden weaknesses early, creating fresh ways to strengthen postures without constant human oversight. This tech wave feels like a game-changer for efficiency.
Challenges
Rapidly Changing Digital Environments
One of the biggest challenges in attack surface management is the rapidly evolving nature of digital environments. With the rise of hybrid work models, increased reliance on cloud services, and the widespread use of IoT devices, organizations face an increasingly complex landscape. New digital assets are continuously being created, which makes it difficult for organizations to maintain an accurate inventory and manage vulnerabilities in real time.
This rapid change introduces gaps in visibility, where unknown or unmanaged assets may remain vulnerable to cyberattacks. Attack surface management solutions need to adapt quickly to the dynamic nature of IT environments, which require continuous monitoring across a wide range of platforms. Overcoming this challenge will require ASM tools that can scale with evolving infrastructures, ensuring that all assets are visible, assessed, and protected against emerging threats.
For instance, in February 2026, Tenable released a report on tracking shifting assets from shadow IT and quick cloud spins, stressing the ongoing chase to map changing perimeters. Security leads wrestle with fresh exposures from unvetted tools, testing their ability to refresh inventories without gaps. It lays bare the grind of staying current in fluid tech landscapes.
Key Players Analysis
In the Attack Surface Management (ASM) market, several prominent players are driving innovation and growth. Cisco Systems, Inc., with its robust cybersecurity portfolio, offers comprehensive solutions for threat intelligence and vulnerability management. CrowdStrike and CyberArk Software Ltd. continue to dominate with their cloud-native endpoint protection and identity security technologies. Their solutions ensure proactive threat detection and risk mitigation, catering to enterprises globally.
International Business Machines Corporation (IBM) and Mandiant are also key players, leveraging advanced AI and machine learning in their ASM tools. Microsoft and Palo Alto Networks provide a wide range of cybersecurity solutions, empowering businesses to continuously monitor and secure their assets. These firms focus on enhancing visibility, threat detection, and compliance across different attack surfaces.
Qualys, Inc., Rapid7, and Tenable, Inc. contribute significantly to vulnerability management, real-time asset discovery, and risk assessment. Their platforms integrate automated patch management and threat intelligence, enhancing security frameworks. Other emerging players also provide specialized services, strengthening the overall competitive landscape of the ASM market. Together, these companies continue to lead the way in shaping the market’s future.
Top Key Players in the Market
- Cisco Systems, Inc.
- CrowdStrike
- CyberArk Software Ltd.
- International Business Machines Corporation
- Mandiant
- Microsoft
- Palo Alto Networks
- Qualys, Inc.
- Rapid7
- Tenable, Inc.
- Others
Recent Developments
- In January 2026, Microsoft integrated advanced ASM features into Defender for Cloud, adding real-time external attack surface monitoring. The solution now scans 25 million assets daily across customer environments. This seamless integration reinforces Microsoft’s position as the go-to ASM platform for 85% of Fortune 500 companies.
- In December 2025, Tenable unveiled Nessus Expert Cloud with ASM capabilities, focusing on OT/ICS environments. The platform discovered 3x more vulnerable industrial assets than legacy scanners. Manufacturing firms reported 60% improvement in risk prioritization, validating Tenable’s specialized approach to expanding attack surfaces.
Report Scope
Report Features Description Market Value (2025) USD 2.3 Bn Forecast Revenue (2035) USD 45.6 Bn CAGR (2026-2035) 34.6% Base Year for Estimation 2025 Historic Period 2020-2024 Forecast Period 2026-2035 Report Coverage Revenue forecast, AI impact on Market trends, Share Insights, Company ranking, competitive landscape, Recent Developments, Market Dynamics and Emerging Trends Segments Covered By Component (Solutions, Services), By Deployment (Cloud, On-premise), By Enterprise Size (SMEs, Large Enterprises), By End Use (BFSI, Healthcare & Life Sciences, Retail & E-commerce, IT & Telecommunications, Government & Public Sector, Manufacturing, Energy & Utilities, Others) Regional Analysis North America – US, Canada; Europe – Germany, France, The UK, Spain, Italy, Russia, Netherlands, Rest of Europe; Asia Pacific – China, Japan, South Korea, India, New Zealand, Singapore, Thailand, Vietnam, Rest of Latin America; Latin America – Brazil, Mexico, Rest of Latin America; Middle East & Africa – South Africa, Saudi Arabia, UAE, Rest of MEA Competitive Landscape Cisco Systems, Inc., CrowdStrike, CyberArk Software Ltd., International Business Machines Corporation, Mandiant, Microsoft, Palo Alto Networks, Qualys, Inc., Rapid7, Tenable, Inc., Others Customization Scope Customization for segments, region/country-level will be provided. Moreover, additional customization can be done based on the requirements. Purchase Options We have three license to opt for: Single User License, Multi-User License (Up to 5 Users), Corporate Use License (Unlimited User and Printable PDF)  Attack Surface Management MarketPublished date: March 2026add_shopping_cartBuy Now get_appDownload Sample
Attack Surface Management MarketPublished date: March 2026add_shopping_cartBuy Now get_appDownload Sample -
-
- Cisco Systems, Inc.
- CrowdStrike
- CyberArk Software Ltd.
- International Business Machines Corporation
- Mandiant
- Microsoft
- Palo Alto Networks
- Qualys, Inc.
- Rapid7
- Tenable, Inc.
- Others