Global Enterprise Key Management Market Size, Share and Analysis Report By Deployment Type (Cloud, On-Premises), By Size of Enterprise (Small- and Medium-sized Enterprises, Large Enterprises), By Application (Disk Encryption, File and Folder Encryption, Database Encryption, Communication Encryption, Cloud Encryption, Others), By End-user Vertical (BFSI, Healthcare, Government and Defense, IT and Telecom, Retail, Other End-user Verticals), By Regional Analysis, Global Trends and Opportunity, Future Outlook By 2025-2035
- Published date: Feb. 2026
- Report ID: 178863
- Number of Pages: 229
- Format:
-
keyboard_arrow_up
Quick Navigation
- Enterprise Key Management Market Size
- Key Takeaways
- Report Overview
- By Deployment Type
- By Size of Enterprise
- By Application
- By End User Vertical
- Regional Analysis
- Key Market Segments
- Emerging Trends Analysis
- Driver Analysis
- Restraint Analysis
- Opportunity Analysis
- Challenge Analysis
- Key Player Analysis
- Recent Developments
- Future Outlook
- Report Scope
Enterprise Key Management Market Size
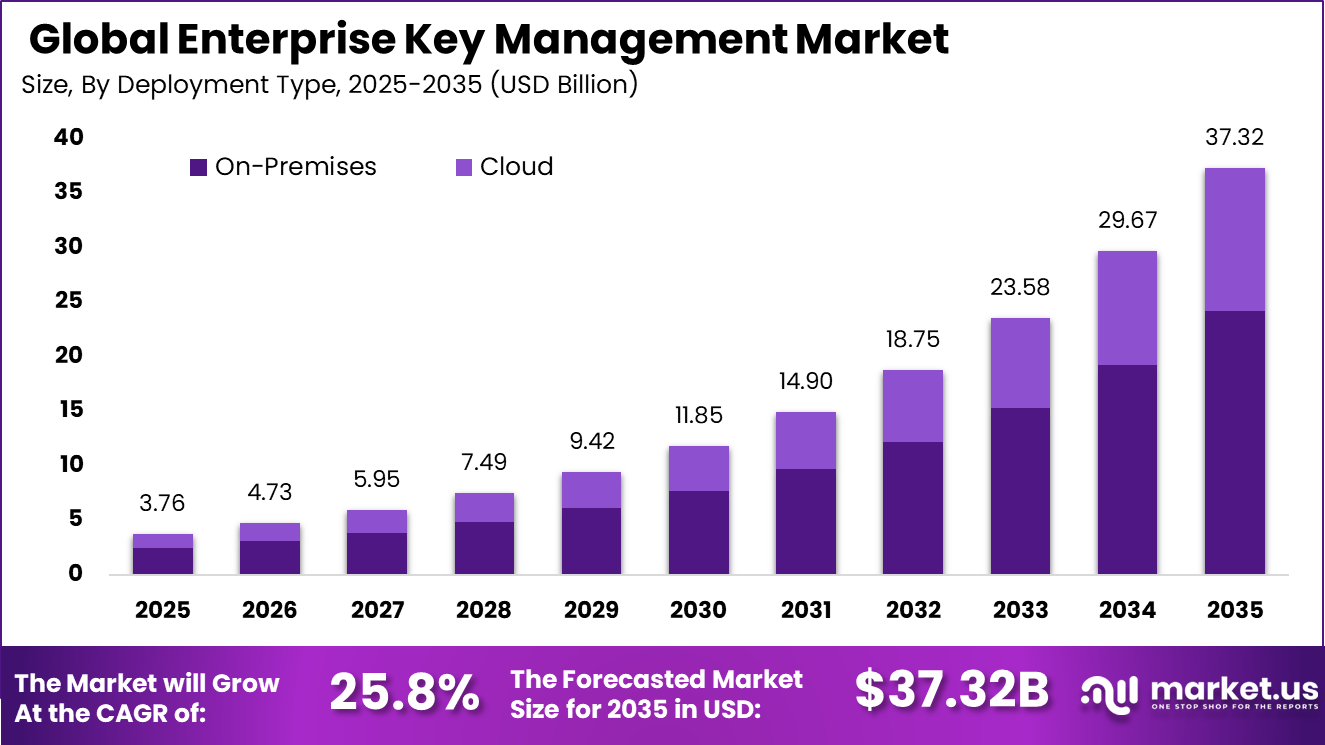
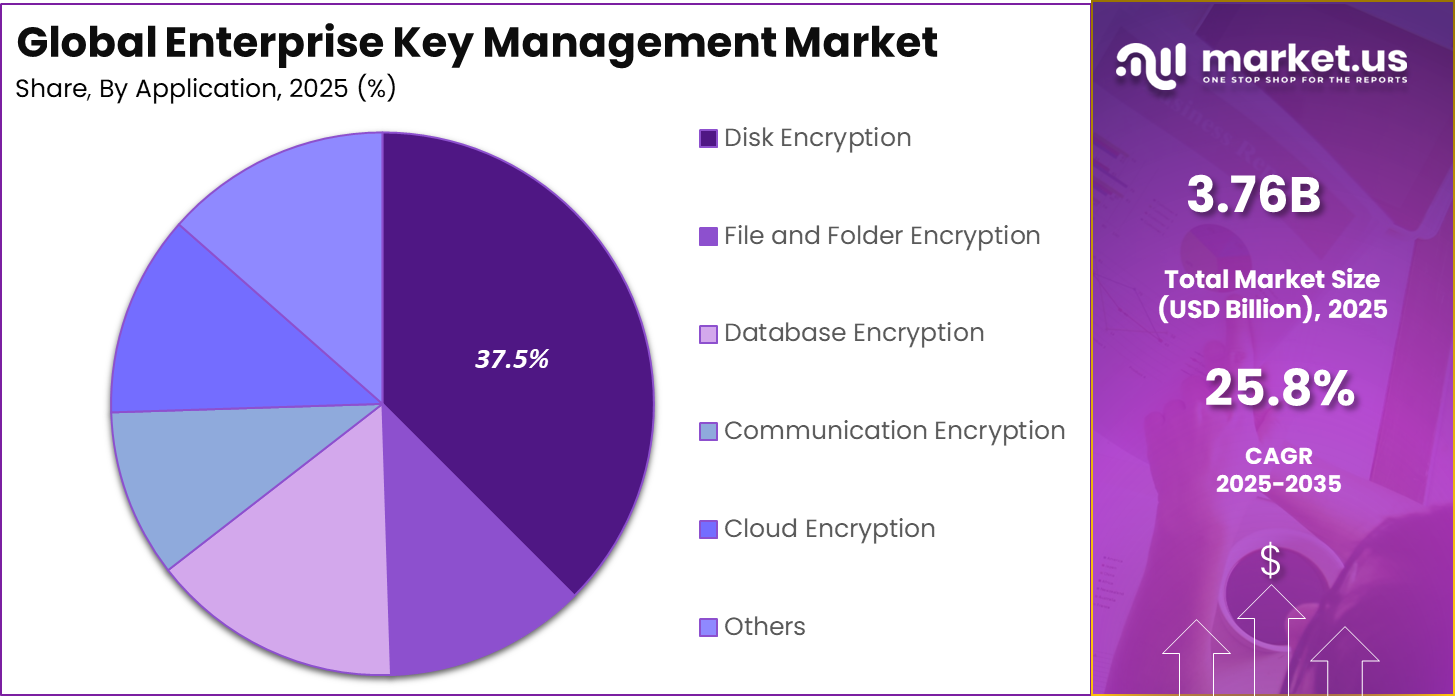
The Global Enterprise Key Management Market size is expected to be worth around USD 37.32 billion by 2035, from USD 3.76 billion in 2025, growing at a CAGR of 25.8% during the forecast period from 2025 to 2035. North America held a dominant market position, capturing more than a 39.2% share, holding USD 1.47 billion in revenue.
Key Takeaways
- The Enterprise Key Management Market is being shaped by rising data protection requirements and regulatory pressure across industries.
- On premises deployment accounts for 64.8% of total adoption, reflecting continued preference for direct control over encryption infrastructure.
- Large enterprises dominate with a share of 73.6%, driven by complex IT environments and higher exposure to cyber risk.
- Disk encryption leads applications with 37.5%, while BFSI remains the largest end user at 38.4% due to strict compliance mandates.
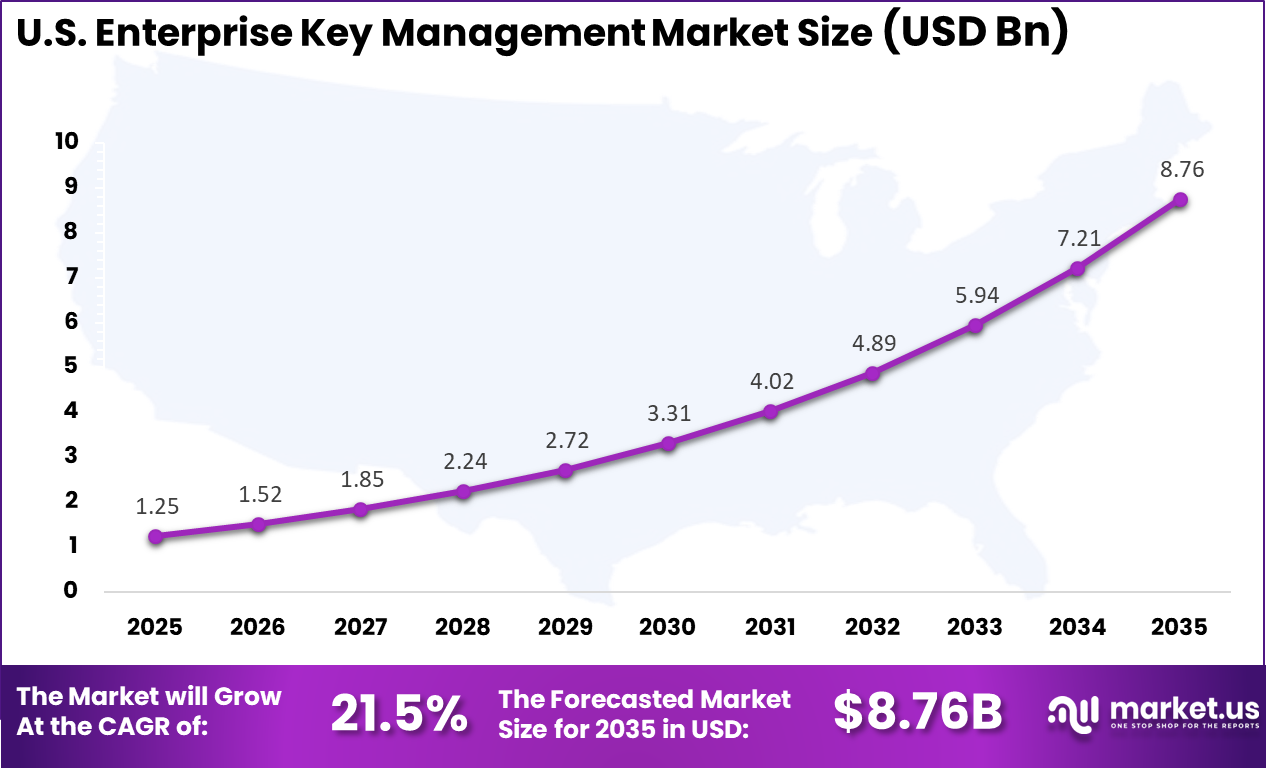
- North America holds 39.2% of the global share, with the United States valued at USD 1.25 Bn and registering a CAGR of 21.5%, indicating strong enterprise level security investments.
- Approximately 48% of enterprises had transitioned portions of their key management operations to hybrid or cloud based Hardware Security Modules as of 2024.
- A 2024 study indicates that nearly 47% of corporate data stored in cloud environments is classified as sensitive.
Report Overview
Enterprise key management refers to centralized systems and policies used to create, store, distribute, rotate, and revoke cryptographic keys across organizational environments. As enterprises increasingly rely on encryption to secure sensitive data, the need for structured and automated key lifecycle management has become essential. Growth in cloud adoption, digital transactions, remote workforce models, and regulatory scrutiny has elevated encryption from a technical feature to a strategic business requirement.
Organizations are focusing on strengthening data confidentiality across endpoints, servers, databases, and cloud platforms. Without proper key management, encryption loses its effectiveness, creating operational and compliance risks. As a result, investment in scalable and interoperable key management solutions has expanded steadily across regulated and data intensive sectors.
The average global cost of a data breach ranged between $4.45 million and $4.88 million in 2024. Enterprise Key Management is widely recognized as a critical control in mitigating financial exposure by strengthening encryption practices and securing sensitive data assets. Approximately 58% of organizations identify integration complexity and high implementation costs as the main barriers to adopting Enterprise Key Management solutions.
By Deployment Type
On premises deployment leads with 64.8% share. Many enterprises, particularly in BFSI and government sectors, prefer to maintain physical control over encryption keys within their internal infrastructure. This approach provides higher visibility, customization, and perceived security control.
Cloud based key management solutions are witnessing increasing traction, especially among mid sized enterprises and digital native companies. Cloud models offer flexibility, faster deployment, and integration with cloud workloads. However, concerns around shared responsibility and regulatory clarity continue to influence deployment decisions.
By Size of Enterprise
Large enterprises account for 73.6% of market demand. These organizations operate across multiple geographies and manage vast volumes of sensitive financial, customer, and operational data. The complexity of their infrastructure necessitates centralized and automated key management platforms.
Small and medium sized enterprises are gradually increasing adoption due to rising cyber threats and affordable cloud based offerings. However, limited cybersecurity budgets and lower compliance pressure compared to large enterprises moderate the adoption pace within this segment.
By Application
Disk encryption represents the leading application with 37.5% share. Enterprises continue to prioritize endpoint and server level encryption to prevent data loss from device theft, unauthorized access, or ransomware incidents. Disk encryption remains a foundational layer in enterprise security architecture.
Database encryption, file and folder encryption, communication encryption, and cloud encryption are also expanding steadily. As structured and unstructured data volumes grow, organizations are deploying multi layer encryption strategies. Cloud encryption in particular is gaining momentum as hybrid and multi cloud environments become common.
By End User Vertical
The BFSI sector holds the largest share at 38.4%. Financial institutions handle highly sensitive transactional and customer data, making encryption key management a compliance and operational necessity. Regulatory frameworks related to payment security, anti money laundering, and data privacy are strengthening demand in this vertical.
Healthcare, government and defense, IT and telecom, and retail sectors are also key contributors. Healthcare organizations are securing patient data and medical records, while government agencies focus on national security and confidential information protection. IT and telecom companies require scalable key management to secure digital services and network infrastructure.
Regional Analysis
North America accounts for 39.2% of the global market. The region benefits from strong cybersecurity awareness, advanced IT infrastructure, and early adoption of cloud technologies. Enterprises in North America allocate significant resources toward encryption and data governance to address sophisticated cyber threats. Strict regulatory frameworks related to financial data, healthcare records, and consumer privacy further support sustained demand.
For instance, in December 2025, AWS launched Amazon EKS Capabilities, integrating AI-driven Kubernetes management with advanced key management for secure AI workloads. This move strengthens enterprise encryption control in hybrid cloud environments, showcasing North American cloud leadership in scalable key protection.
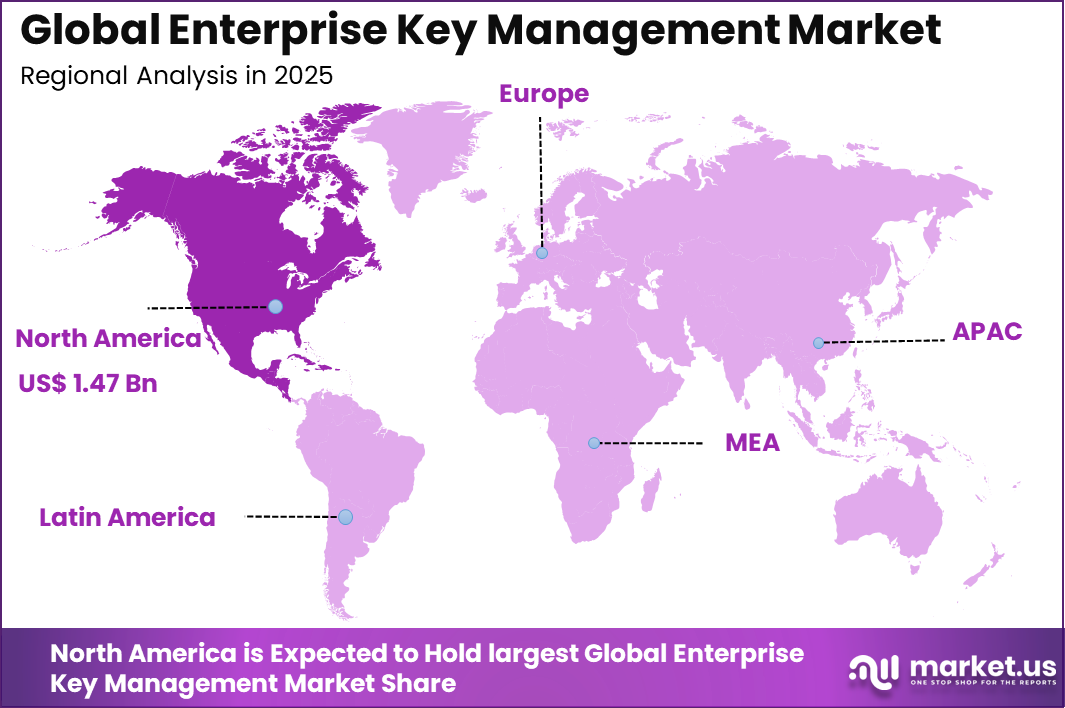
The United States represents the largest contributor within North America, valued at USD 1.25 Bn and expanding at a CAGR of 21.5%. High concentration of financial institutions, technology companies, and federal agencies strengthens demand for advanced key management platforms. Ongoing investments in cloud security, digital banking, and zero trust architectures are reinforcing the importance of centralized cryptographic governance across U.S. enterprises.
Key Market Segments
By Deployment Type
- Cloud
- On-Premises
By Size of Enterprise
- Small- and Medium-sized Enterprises
- Large Enterprises
By Application
- Disk Encryption
- File and Folder Encryption
- Database Encryption
- Communication Encryption
- Cloud Encryption
- Others
By End-user Vertical
- BFSI
- Healthcare
- Government and Defense
- IT and Telecom
- Retail
- Other End-user Verticals
Regional Analysis and Coverage
- North America
- US
- Canada
- Europe
- Germany
- France
- The UK
- Spain
- Italy
- Russia
- Netherlands
- Rest of Europe
- Asia Pacific
- China
- Japan
- South Korea
- India
- Australia
- Singapore
- Thailand
- Vietnam
- Rest of Latin America
- Latin America
- Brazil
- Mexico
- Rest of Latin America
- Middle East & Africa
- South Africa
- Saudi Arabia
- UAE
- Rest of MEA
Emerging Trends Analysis
The Enterprise Key Management market is evolving with the increasing adoption of centralized and cloud integrated key management platforms. Organizations are moving away from fragmented encryption key storage toward unified systems that manage keys across cloud, on premises, and hybrid environments.
This transition supports consistent encryption policies and simplifies lifecycle management of cryptographic keys. As enterprises expand multi cloud deployments, centralized visibility and automated key rotation are becoming standard requirements. Another emerging trend is the integration of hardware security modules and confidential computing frameworks within key management solutions.
Enterprises are prioritizing stronger root of trust mechanisms to protect sensitive workloads and encrypted data. Advanced key orchestration tools are being embedded within DevOps pipelines to secure application development environments. This alignment between security and digital transformation initiatives is strengthening demand for scalable key management infrastructure.
Driver Analysis
A primary driver of the Enterprise Key Management market is the rapid growth of data encryption across enterprise IT environments. Organizations are encrypting databases, storage systems, endpoints, and communication channels to safeguard sensitive information. As encryption volumes increase, the complexity of managing keys also expands.
Dedicated key management platforms are therefore essential to ensure availability, compliance, and operational efficiency. Another major driver is the tightening regulatory landscape related to data protection and cybersecurity. Compliance requirements across financial services, healthcare, and government sectors mandate strong encryption and secure key handling practices.
For instance, in March 2025, AWS KMS faced the spotlight in ransomware attacks like RansomWhen, where attackers exploited key material imports to lock data. The service shone for its integration and logging, but highlighted needs for tighter policies on key uploads and deletions. It underscores how central key tools are to bolster defenses against evolving cyber dangers.
Restraint Analysis
One key restraint in the market is the complexity associated with integrating key management systems into legacy IT infrastructure. Many enterprises operate heterogeneous environments with varied encryption standards and legacy applications. Aligning these systems under a unified key management framework requires customization and technical expertise. This complexity can delay deployment and increase implementation costs.
Another restraint involves the high operational overhead of managing cryptographic keys at scale. Key lifecycle processes such as generation, distribution, rotation, and revocation require strict controls and continuous monitoring. Smaller enterprises may lack specialized personnel to manage these tasks effectively. Resource limitations can therefore slow broader adoption.
For instance, in September 2021, IBM tools like EKMF lack full unified features for hybrid clouds, forcing manual key imports that eat time and staff effort. Splitting functionalities across products adds layers of complexity, making smooth implementation a grind for banking teams. It points to ongoing hurdles in resource-heavy deployments.
Opportunity Analysis
A significant opportunity lies in the expansion of key management services within cloud native and containerized environments. As enterprises modernize applications and adopt microservices architectures, secure key storage and automated orchestration become critical. Vendors that provide API driven and DevSecOps compatible key management platforms can capture growing demand.
Integration with container orchestration systems enhances security within dynamic environments. Another opportunity exists in the adoption of post quantum cryptography planning and advanced encryption frameworks. Enterprises are beginning to assess long term cryptographic resilience strategies. Key management solutions that support algorithm agility and future ready encryption standards can differentiate in the market.
For instance, in November 2025, HashiCorp Vault enhanced multi-cloud key handling across AWS, Azure, Google Cloud, and on-prem with one workflow for rotation and lifecycle. It taps cloud KMS strengths while centralizing control, fitting hybrid shifts perfectly. Teams gain speed and cut hardware costs in spread-out IT landscapes.
Challenge Analysis
A primary challenge in the Enterprise Key Management market is maintaining uninterrupted key availability while ensuring strict security controls. Downtime or mismanagement of keys can disrupt encrypted applications and business operations. Balancing resilience with protection requires robust redundancy and backup mechanisms. Achieving this balance demands careful architectural planning.
Another challenge involves mitigating insider threats and unauthorized access to sensitive cryptographic material. Privileged users with excessive access rights can create internal security risks. Implementing strong access governance, role based controls, and audit logging is essential. Continuous monitoring and policy enforcement remain critical to maintaining enterprise trust in encryption systems.
For instance, in September 2025, Keyfactor’s research exposed weekly certificate outages tied to missing automation skills and integration woes in 45% of cases. Leaders noted gaps in internal expertise blocking proactive management, risking operations and trust. It calls out the talent crunch hitting digital security efforts hard.
Key Player Analysis
The competitive landscape is characterized by global technology providers and specialized encryption security firms. Amazon Web Services, Inc., Google LLC, and Microsoft Corporation offer integrated cloud native key management services embedded within their broader cloud ecosystems. These providers focus on scalability, automation, and seamless integration with enterprise workloads.
Thales Group, International Business Machines Corporation, Oracle Corporation, and Hewlett Packard Enterprise Company provide enterprise grade encryption and hardware security modules tailored for regulated industries. Their strength lies in deep security expertise, compliance alignment, and hybrid deployment capabilities.
Specialized vendors such as Venafi, Inc., HashiCorp, Inc., Entrust Corporation, Fortanix Inc., Keyfactor, Inc., nCipher Security, LLC, WinMagic Inc., ESCRYPT GmbH, HyTrust, Inc., CipherCloud, Inc., Quantum Corporation, Dell Technologies Inc., and Micro Focus International plc focus on certificate lifecycle management, cloud key protection, and advanced cryptographic services. These companies compete through innovation in automation, interoperability, and policy driven key management solutions.
Top Key Players in the Market
- Amazon Web Services, Inc.
- Venafi, Inc.
- Thales Group
- Google LLC
- International Business Machines Corporation
- Oracle Corporation
- Hewlett Packard Enterprise Company
- Quantum Corporation
- WinMagic Inc.
- Microsoft Corporation
- Dell Technologies Inc.
- HashiCorp, Inc.
- Micro Focus International plc
- Entrust Corporation
- Fortanix Inc.
- ESCRYPT GmbH
- Keyfactor, Inc.
- nCipher Security, LLC
- HyTrust, Inc.
- CipherCloud, Inc.
- Others
Recent Developments
- In October 2025, Oracle rolled out the External Key Management System (EKMS) supporting Thales CipherTrust for Fusion Cloud, enabling BYOK/HYOK workflows. This partnership delivers sovereign encryption control, reinforcing enterprise data protection standards globally.
- In October 2025, IBM unveiled Guardium Cryptography Manager, an AI-powered tool for quantum-resilient key and certificate management across hybrid clouds. Starting in November, it integrates with HashiCorp Vault, addressing crypto-agility needs for regulated enterprises.
Future Outlook
The Enterprise Key Management Market is expected to maintain strong momentum as encryption becomes foundational to digital business models. Increasing digital transactions, remote work models, and connected devices will continue to expand the need for secure key lifecycle management.
Greater automation, artificial intelligence based threat monitoring, and integration with zero trust security frameworks are expected to enhance solution capabilities. As regulatory expectations strengthen globally, enterprise key management will remain a critical component of corporate cybersecurity strategy.
Report Scope
Report Features Description Market Value (2025) USD 3.7 Bn Forecast Revenue (2035) USD 37.3 Bn CAGR(2026-2035) 25.8% Base Year for Estimation 2025 Historic Period 2020-2024 Forecast Period 2026-2035 Report Coverage Revenue forecast, AI impact on Market trends, Share Insights, Company ranking, competitive landscape, Recent Developments, Market Dynamics and Emerging Trends Segments Covered By Deployment Type (Cloud, On-Premises), By Size of Enterprise (Small- and Medium-sized Enterprises, Large Enterprises), By Application (Disk Encryption, File and Folder Encryption, Database Encryption, Communication Encryption, Cloud Encryption, Others), By End-user Vertical (BFSI, Healthcare, Government and Defense, IT and Telecom, Retail, Other End-user Verticals) Regional Analysis North America – US, Canada; Europe – Germany, France, The UK, Spain, Italy, Russia, Netherlands, Rest of Europe; Asia Pacific – China, Japan, South Korea, India, New Zealand, Singapore, Thailand, Vietnam, Rest of Latin America; Latin America – Brazil, Mexico, Rest of Latin America; Middle East & Africa – South Africa, Saudi Arabia, UAE, Rest of MEA Competitive Landscape Amazon Web Services, Inc., Venafi, Inc., Thales Group, Google LLC, International Business Machines Corporation, Oracle Corporation, Hewlett Packard Enterprise Company, Quantum Corporation, WinMagic Inc., Microsoft Corporation, Dell Technologies Inc., HashiCorp, Inc., Micro Focus International plc, Entrust Corporation, Fortanix Inc., ESCRYPT GmbH, Keyfactor, Inc., nCipher Security, LLC, HyTrust, Inc., CipherCloud, Inc., Others Customization Scope Customization for segments, region/country-level will be provided. Moreover, additional customization can be done based on the requirements. Purchase Options We have three license to opt for: Single User License, Multi-User License (Up to 5 Users), Corporate Use License (Unlimited User and Printable PDF)  Enterprise Key Management MarketPublished date: Feb. 2026add_shopping_cartBuy Now get_appDownload Sample
Enterprise Key Management MarketPublished date: Feb. 2026add_shopping_cartBuy Now get_appDownload Sample -
-
- Amazon Web Services, Inc.
- Venafi, Inc.
- Thales Group
- Google LLC
- International Business Machines Corporation
- Oracle Corporation
- Hewlett Packard Enterprise Company
- Quantum Corporation
- WinMagic Inc.
- Microsoft Corporation
- Dell Technologies Inc.
- HashiCorp, Inc.
- Micro Focus International plc
- Entrust Corporation
- Fortanix Inc.
- ESCRYPT GmbH
- Keyfactor, Inc.
- nCipher Security, LLC
- HyTrust, Inc.
- CipherCloud, Inc.
- Others