Global Operational Technology (OT) Security Market Size, Share and Analysis Report By Component (Solutions, Services), By Deployment Mode (On-Premises, Cloud), By End-User Industry (Manufacturing, Oil and Gas, Power Utilities, Transportation and Logistics, Chemicals and Pharma, Mining and Metals, Others), By Security Layer (Network Monitoring and Anomaly Detection, Endpoint / Device Security, Identity and Access Management, Secure Remote Access and Segmentation Gateways, Governance, Risk and Compliance Platforms), By Regional Analysis, Global Trends and Opportunity, Future Outlook By 2025-2035
- Published date: Feb. 2026
- Report ID: 136724
- Number of Pages: 316
- Format:
-
keyboard_arrow_up
Quick Navigation
- Report Overview
- Top Market Takeaways
- Key Insights
- By Component: Solutions
- By Deployment Mode: On-Premises
- By End-User Industry: Manufacturing
- By Security Layer: Network Monitoring
- Regional Overview: North America
- Emerging Trends Analysis
- Key Market Segments
- Driver Analysis
- Restraint Analysis
- Opportunity Analysis
- Challenge Analysis
- Competitive Analysis
- Recent Developments
- Report Scope
Report Overview
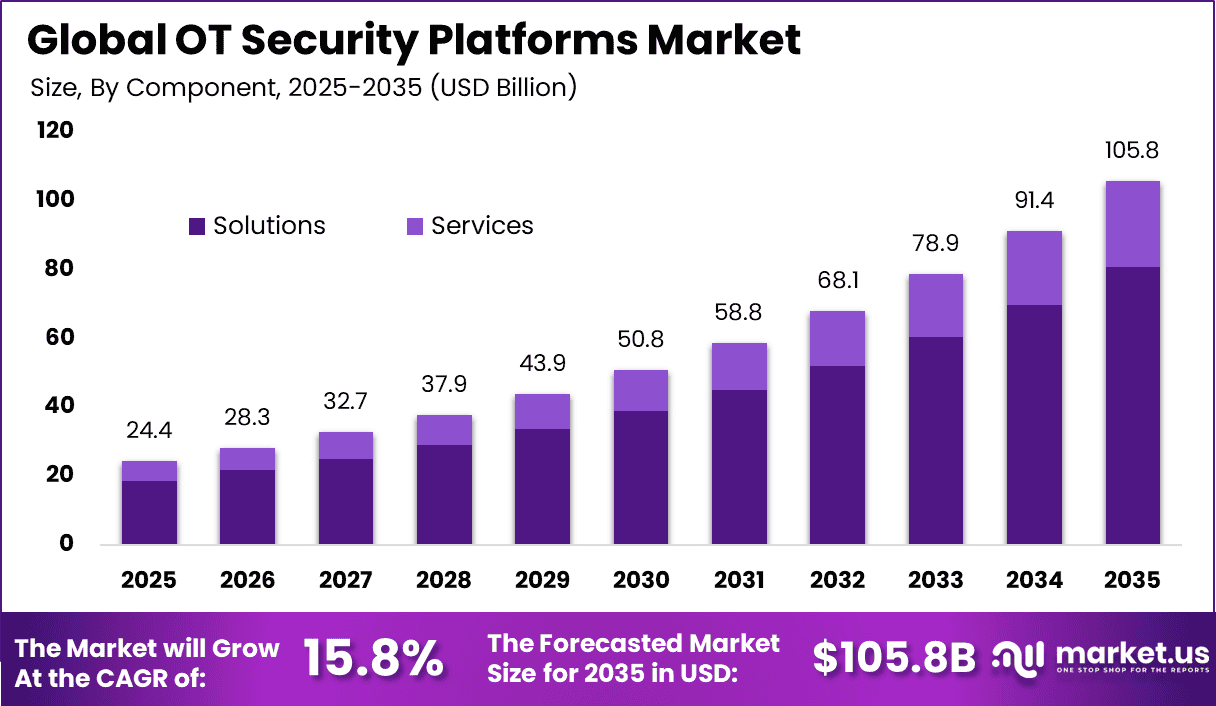
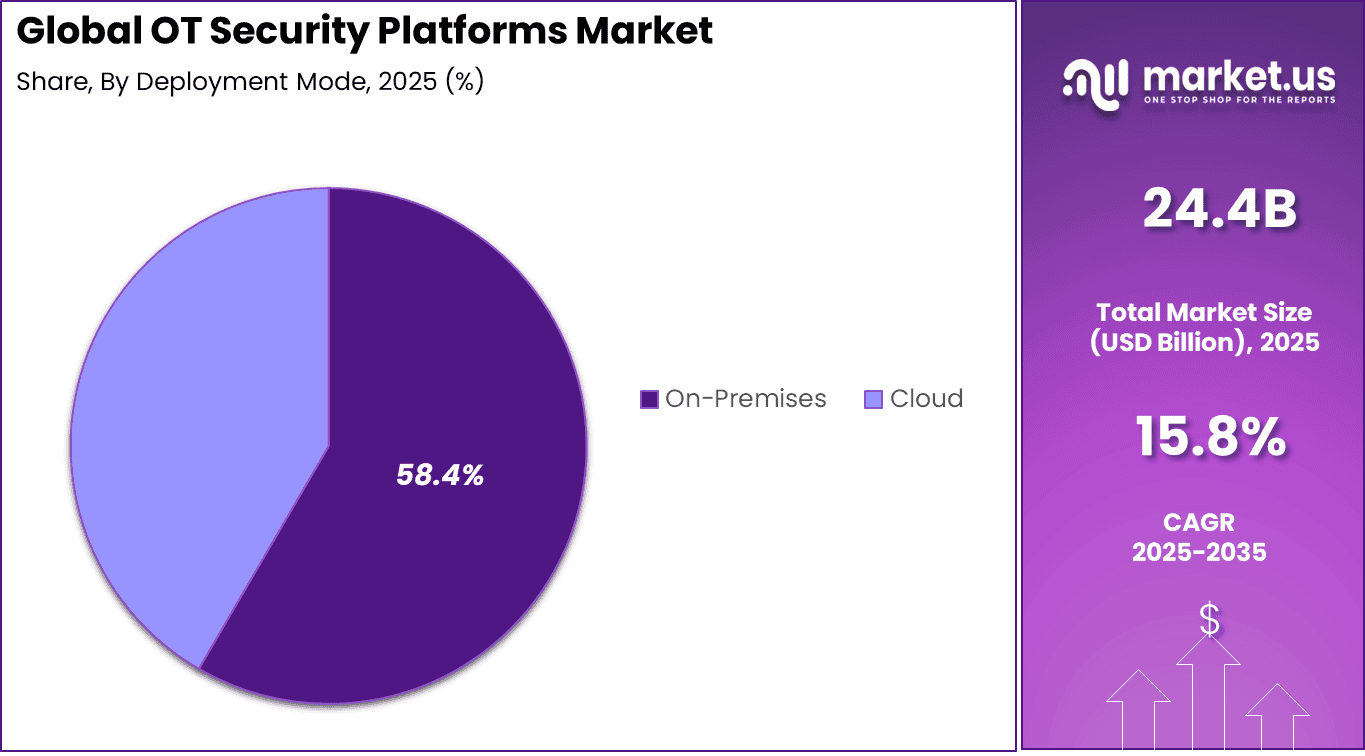
The Global OT Security Platforms Market size is expected to be worth around USD 105.8 Billion By 2035, from USD 24.4 billion in 2025, growing at a CAGR of 15.8% during the forecast period from 2026 to 2035. North America held a dominant Market position, capturing more than a 39.7% share, holding USD 9.6 Billion revenue.
The OT Security Platforms Market refers to technologies and solutions that protect operational technology environments used in industrial, manufacturing, energy, and critical infrastructure sectors. These platforms are designed to monitor, detect, and respond to cyber threats targeting systems such as industrial control systems, programmable logic controllers, and supervisory control and data acquisition systems.
Operational technology networks operate physical processes, and security solutions tailored to this domain provide visibility into assets, communication flows, and threat patterns. As industry digitization increases, the need for robust OT security has become essential to maintain safe and reliable operations. Growth in this market is supported by the convergence of information technology and operational technology networks.
Traditional security tools are often inadequate for OT environments due to differences in protocols, real time constraints, and risk tolerance. OT security platforms offer specialized capabilities to address these challenges, including anomaly detection, asset inventory, network segmentation, and incident response workflows. As industrial organizations adopt digital technologies, ensuring the resilience and integrity of OT assets has become a strategic priority, contributing to sustained market expansion.
A key driving factor for the OT Security Platforms Market is the increasing frequency and sophistication of cyberattacks targeting industrial environments. Threat actors have demonstrated the ability to disrupt production processes, compromise safety systems, and cause operational downtime. High profile incidents have underscored the potential impact on public safety and business continuity.
Demand for OT security platforms is particularly strong among industries with large and complex operational networks. Energy and utilities companies prioritize solutions that can secure distributed assets, remote stations, and legacy control systems. Manufacturing enterprises require visibility into production lines, machine communications, and interconnected systems. Telecommunications and transportation sectors also seek technologies that can safeguard critical operational infrastructure.
Top Market Takeaways
- Solutions accounted for 76.5% of the OT Security Platforms market, reflecting strong demand for integrated threat detection, asset visibility, and centralized risk management systems.
- On-premises deployment led with 58.4% share, supported by strict data governance requirements and the need for direct control over industrial security environments.
- Manufacturing represented 38.7% of total demand, driven by increasing protection needs for industrial control systems and connected production assets.
- Network monitoring and anomaly detection held 40.6% share, as continuous traffic inspection and behavioral analytics remain critical for operational continuity.
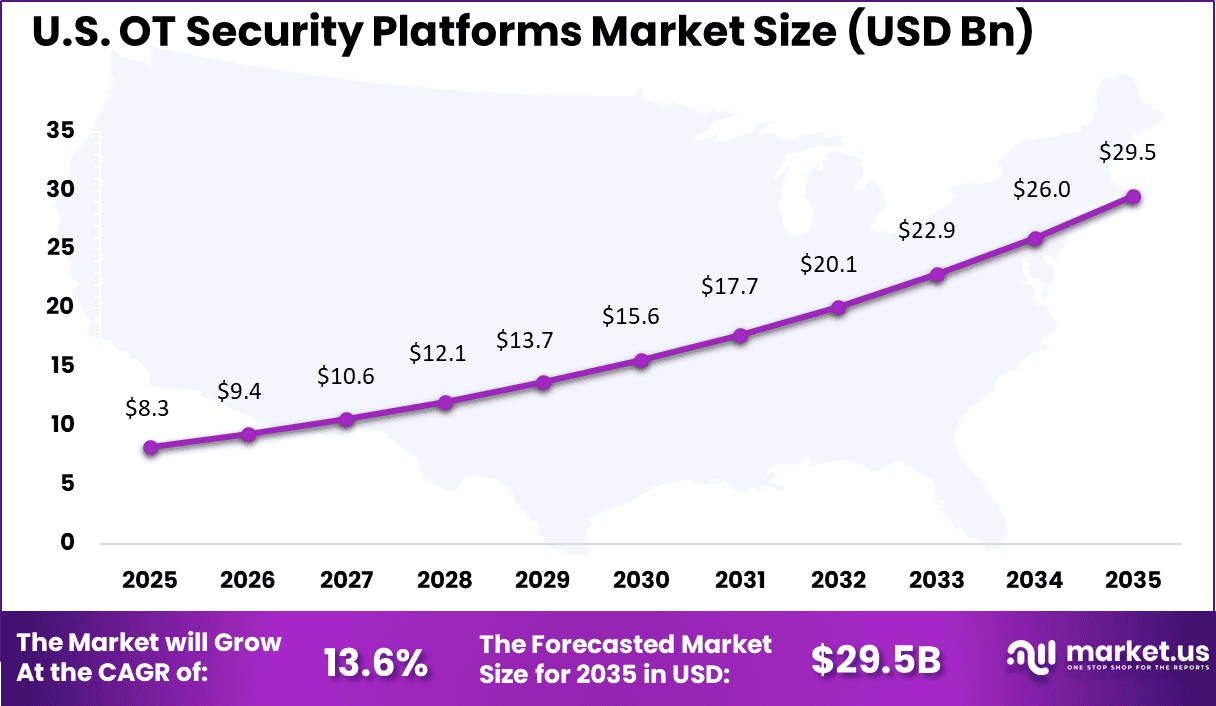
- North America captured 39.7% of the market, with the United States generating USD 8.25 billion in revenue and expanding at a 13.6% CAGR, supported by high cybersecurity investments across critical infrastructure sectors.
Key Insights
- More than 12,000 cybersecurity incidents targeting industrial control systems were reported globally in 2024, indicating sustained threat activity across critical infrastructure environments.
- Around 75% of OT organizations experienced at least one system intrusion during the past year, highlighting persistent exposure across operational networks.
- OT-related breaches resulted in an average financial impact of USD 4.56 million per incident, exceeding the global average cost of conventional data breaches due to operational downtime and recovery expenses.
- In the first half of 2025, 49% of disclosed OT vulnerabilities were classified as Critical or High severity, reflecting elevated risk across legacy and connected systems.
- Manufacturing remained the most targeted industry, accounting for 17% of total targeted attacks, driven by its reliance on interconnected production assets.
- Executive oversight has increased significantly, with 52% of organizations assigning direct OT security responsibility to the CISO or CSO, compared to 16% in 2022.
- Approximately 81% of organizations rate their OT security maturity at Level 3 or 4 on a five-point scale. Among Level 4 organizations, 65% reported zero intrusions, indicating stronger governance and control frameworks.
- Vendor consolidation is progressing, as 78% of enterprises now operate with four or fewer OT security vendors to reduce integration complexity and improve operational efficiency.
- On-premises deployments continue to represent 58% to 60% of total installations. However, cloud-based OT security accounts for 40% to 42% of new deployments, making it the fastest-growing implementation model.
By Component: Solutions
Solutions account for 76.5% of the Operational Technology security market. Industrial environments require specialized cybersecurity platforms designed to protect control systems, programmable logic controllers, and supervisory control networks. These solutions provide asset discovery, threat detection, vulnerability assessment, and incident response capabilities tailored for OT infrastructure. As cyber threats increasingly target critical infrastructure, demand for dedicated OT security solutions continues to expand.
OT environments differ significantly from traditional IT systems, requiring minimal disruption and high system availability. Security solutions are designed to operate without interrupting production processes. Continuous monitoring and risk assessment tools help identify vulnerabilities before exploitation occurs. Integration with industrial control systems enhances visibility across operational networks. The growing need for resilience in critical operations explains the dominant share of solutions.
By Deployment Mode: On-Premises
On-premises deployment represents 58.4% of the OT security market. Many industrial operators prefer localized security control due to strict reliability and safety requirements. On-premises systems allow direct oversight of sensitive infrastructure without reliance on external cloud connectivity. This approach reduces latency and ensures uninterrupted monitoring of industrial processes. It is particularly important in sectors where downtime can cause significant operational disruption.
Industrial facilities often operate legacy equipment that requires customized security integration. On-premises deployment provides flexibility to adapt security controls to unique plant environments. Data sovereignty and regulatory compliance considerations further support localized deployments. Organizations managing critical infrastructure prioritize internal control over security configurations. These factors contribute to the strong presence of on-premises solutions.
By End-User Industry: Manufacturing
Manufacturing accounts for 38.7% of the OT security market. Modern manufacturing facilities rely heavily on connected machinery and automated production lines. As factories integrate industrial internet technologies, exposure to cyber risks increases. OT security solutions help protect production systems from ransomware, unauthorized access, and operational disruption. Ensuring continuous production and equipment safety remains a primary priority.
Manufacturers also face supply chain vulnerabilities that require enhanced network protection. Real-time monitoring of industrial assets helps detect abnormal activity and prevent downtime. Regulatory standards related to industrial safety further drive security investments. Integration of OT and IT networks increases the need for comprehensive visibility. The sector’s high automation level explains its significant market share.
By Security Layer: Network Monitoring
Network monitoring and anomaly detection hold 40.6% of the security layer segment. Continuous monitoring of industrial network traffic is essential to identify suspicious behavior. Anomaly detection systems analyze communication patterns between devices and flag deviations from established baselines. This proactive approach helps detect threats before they disrupt operations. Early identification reduces the likelihood of large-scale production interruptions.
Industrial networks often include legacy protocols that lack built-in security features. Monitoring tools compensate by providing visibility into device interactions and traffic flows. Advanced analytics enhance detection accuracy and minimize false positives. These capabilities are critical for safeguarding critical infrastructure environments. The emphasis on real-time threat detection supports the strong adoption of this security layer.
Regional Overview: North America
North America accounts for 39.7% of the global OT security market. The region demonstrates high investment in critical infrastructure protection and industrial cybersecurity frameworks. Organizations across energy, manufacturing, and utilities sectors prioritize securing operational networks. Increasing regulatory oversight further strengthens demand for comprehensive OT security platforms. This supports steady regional market expansion.
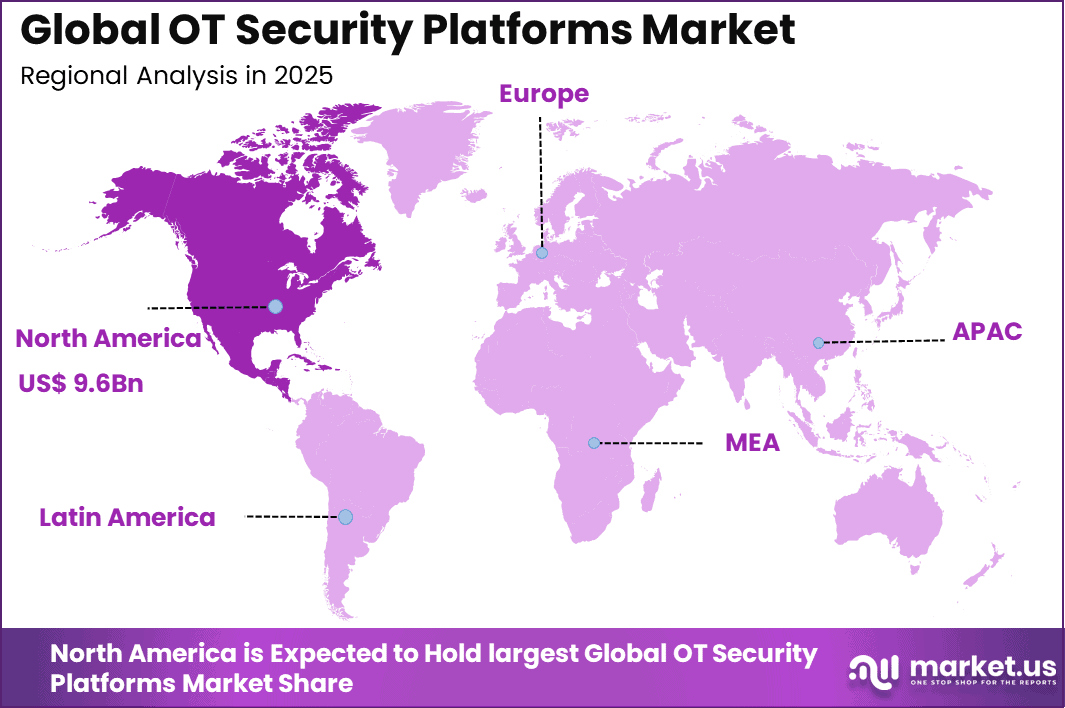
The United States leads regional growth with a market value of USD 8.25 Bn and a CAGR of 13.6%. Industrial modernization initiatives and digital transformation programs continue to expand attack surfaces. Enterprises are investing in advanced monitoring and threat detection systems to enhance resilience. Strong collaboration between public and private sectors supports cybersecurity advancement. North America remains a key region for OT security deployment and innovation.
Emerging Trends Analysis
A key trend shaping the Operational Technology (OT) Security market is the increasing integration of artificial intelligence (AI) and hybrid security architectures to address complex industrial cyber risks. As industrial environments evolve, security frameworks are shifting toward hybrid models that combine centralized cloud visibility with decentralized on-site protections, enabling real-time threat detection across both traditional IT and OT systems.
This transition is driven by the need to support heterogeneous environments that include legacy controllers, smart sensors, and internet-connected devices, expanding the scope of security operations beyond isolated network segments. As these hybrid approaches mature, OT security strategies are becoming more adaptive and resilient against sophisticated attacks.
The trend toward zero-trust microsegmentation is also becoming prominent within OT security practices. Traditional perimeter-based defenses are being replaced with architectures that assume potential compromise at every network point, requiring strict access controls and continuous verification of devices and users. This approach is particularly relevant in industrial settings where the convergence of IT and OT has increased the attack surface and exposed critical control systems to broader cyber threats.
Key Market Segments
By Component
- Solutions
- Services
By Deployment Mode
- On-Premises
- Cloud
By End-User Industry
- Manufacturing
- Oil and Gas
- Power Utilities
- Transportation and Logistics
- Chemicals and Pharma
- Mining and Metals
- Others
By Security Layer
- Network Monitoring and Anomaly Detection
- Endpoint / Device Security
- Identity and Access Management
- Secure Remote Access and Segmentation Gateways
- Governance, Risk and Compliance Platforms
- Others
Regional Analysis and Coverage
- North America
- US
- Canada
- Europe
- Germany
- France
- The UK
- Spain
- Italy
- Russia
- Netherlands
- Rest of Europe
- Asia Pacific
- China
- Japan
- South Korea
- India
- Australia
- Singapore
- Thailand
- Vietnam
- Rest of Latin America
- Latin America
- Brazil
- Mexico
- Rest of Latin America
- Middle East & Africa
- South Africa
- Saudi Arabia
- UAE
- Rest of MEA
Driver Analysis
The primary driver of the OT security market is the rising frequency of cyberattacks targeting critical infrastructure and industrial systems. Sectors such as energy, manufacturing, utilities, and transportation are increasingly exposed due to expanded digital connectivity. Disruptions to these systems can result in financial losses, operational downtime, and public safety risks. This risk exposure is accelerating investment in specialized OT security solutions.
Another key driver is the expansion of Industry 4.0 initiatives and smart manufacturing deployments. Industrial automation, connected sensors, and remote monitoring systems increase network complexity and vulnerability. As enterprises modernize production environments, protecting programmable logic controllers and supervisory control systems becomes essential. Security investment is therefore being integrated into broader digital transformation budgets.
Restraint Analysis
One major restraint in the OT security market is the shortage of skilled professionals with expertise in industrial cybersecurity. OT environments differ significantly from traditional IT systems and require specialized knowledge of industrial protocols and control systems. Many organizations face challenges in recruiting and retaining such expertise. This skills gap can delay implementation and limit the effectiveness of deployed solutions.
High deployment costs also restrict broader adoption, particularly among mid sized industrial enterprises. Integrating modern security solutions into legacy control systems often requires customization and extended testing cycles. Budget constraints can slow replacement of outdated infrastructure that lacks native security features. As a result, some organizations postpone upgrades despite rising threat levels.
Opportunity Analysis
A significant opportunity exists in managed OT security services and cloud based monitoring platforms. Many industrial enterprises prefer outsourcing complex security operations to specialized providers. Managed services offer continuous monitoring, rapid incident response, and regulatory compliance support. This model reduces internal resource strain and supports scalable protection.
Emerging markets undergoing rapid industrialization present additional growth potential. Expansion of smart grids, automated manufacturing plants, and digital oil and gas facilities increases the need for secure operational environments. Governments are prioritizing cybersecurity frameworks to protect national infrastructure. Vendors that localize solutions and provide compliance aligned offerings can capture expanding regional demand.
Challenge Analysis
A major challenge is securing legacy industrial systems that were not originally designed with cybersecurity in mind. Many operational assets operate on outdated software and proprietary protocols. Replacing these systems can disrupt production and require substantial capital investment. Balancing operational continuity with security upgrades remains complex.
Another challenge involves maintaining visibility across highly distributed and heterogeneous environments. Industrial networks often span multiple sites with varied equipment vendors and configurations. Achieving unified monitoring and centralized policy enforcement can be technically demanding. Without comprehensive visibility, detecting and responding to threats becomes more difficult.
Competitive Analysis
The OT Security Platforms market includes established players such as NEC Corporation, Thales Group, and IDEMIA. These companies provide integrated cybersecurity and identity management solutions for critical infrastructure. Their platforms support secure remote access, network segmentation, and industrial asset protection. Strong global presence and long-term government contracts strengthen their competitive position.
Firms such as Aware, Inc., Cognitec Systems, and Ayonix Corporation contribute biometric authentication capabilities that enhance access control within operational technology environments. Technology-driven providers including Herta Security, FaceFirst, VisionLabs, and Oosto focus on AI-powered monitoring and threat detection. Their solutions enable real-time analytics across industrial facilities and high-risk infrastructure sites.
SenseTime, Megvii, and ZKTeco deliver scalable facial recognition and workforce authentication systems. These technologies are increasingly integrated into OT frameworks to strengthen physical and digital security alignment. Continuous innovation in computer vision and AI modeling supports higher detection accuracy and faster response times.
Emerging vendors such as Innovatrics, Tech5, BioID, Veridas, Clearview AI, and Camvi Technologies offer specialized biometric and identity verification solutions. Their platforms are used for contractor validation, secure onboarding, and compliance-driven access management. Many of these companies focus on cloud-based a
Top Key Players in the Market
- NEC Corporation
- Thales Group
- IDEMIA
- Cognitec Systems
- Ayonix Corporation
- Herta Security
- FaceFirst
- Aware, Inc.
- VisionLabs
- AnyVision (now Oosto)
- Trueface
- SenseTime
- Megvii (Face++)
- ZKTeco
- Innovatrics
- Tech5
- BioID
- Veridas
- Clearview AI
- Camvi Technologies
- Others
Recent Developments
- In April 2025, OT Cyber Direct introduced a digital marketplace focused on delivering validated and cost-efficient Operational Technology security solutions for small and medium-sized businesses. The platform has been developed to simplify access to trusted OT security applications and support organizations in strengthening the protection of their industrial environments.
- In March 2025, Armis, a cyber exposure management and security provider, announced the acquisition of OTORIO, a specialist in Operational Technology and Cyber Physical Systems security. The transaction is intended to enhance Armis’ capabilities in securing industrial and connected environments.
Report Scope
Report Features Description Market Value (2025) USD 24.4 Bn Forecast Revenue (2035) USD 105.8 Bn CAGR(2026-2035) 15.8% Base Year for Estimation 2025 Historic Period 2020-2024 Forecast Period 2026-2035 Report Coverage Revenue forecast, AI impact on Market trends, Share Insights, Company ranking, competitive landscape, Recent Developments, Market Dynamics and Emerging Trends Segments Covered By Component (Solutions, Services), By Deployment Mode (On-Premises, Cloud), By End-User Industry (Manufacturing, Oil and Gas, Power Utilities, Transportation and Logistics, Chemicals and Pharma, Mining and Metals, Others), By Security Layer (Network Monitoring and Anomaly Detection, Endpoint / Device Security, Identity and Access Management, Secure Remote Access and Segmentation Gateways, Governance, Risk and Compliance Platforms) Regional Analysis North America – US, Canada; Europe – Germany, France, The UK, Spain, Italy, Russia, Netherlands, Rest of Europe; Asia Pacific – China, Japan, South Korea, India, New Zealand, Singapore, Thailand, Vietnam, Rest of Latin America; Latin America – Brazil, Mexico, Rest of Latin America; Middle East & Africa – South Africa, Saudi Arabia, UAE, Rest of MEA Competitive Landscape NEC Corporation, Thales Group, IDEMIA, Cognitec Systems, Ayonix Corporation, Herta Security, FaceFirst, Aware, Inc., VisionLabs, AnyVision (now Oosto), Trueface, SenseTime, Megvii (Face++), ZKTeco, Innovatrics, Tech5, BioID, Veridas, Clearview AI, Camvi Technologies, Others Customization Scope Customization for segments, region/country-level will be provided. Moreover, additional customization can be done based on the requirements. Purchase Options We have three license to opt for: Single User License, Multi-User License (Up to 5 Users), Corporate Use License (Unlimited User and Printable PDF)  Operational Technology (OT) Security MarketPublished date: Feb. 2026add_shopping_cartBuy Now get_appDownload Sample
Operational Technology (OT) Security MarketPublished date: Feb. 2026add_shopping_cartBuy Now get_appDownload Sample -
-
- NEC Corporation
- Thales Group
- IDEMIA
- Cognitec Systems
- Ayonix Corporation
- Herta Security
- FaceFirst
- Aware, Inc.
- VisionLabs
- AnyVision (now Oosto)
- Trueface
- SenseTime
- Megvii (Face++)
- ZKTeco
- Innovatrics
- Tech5
- BioID
- Veridas
- Clearview AI
- Camvi Technologies
- Others