Global Zero Trust Network Access Market Size, Share and Analysis By Component (Solution, Services), By Deployment (Cloud, On-Premise, Hybrid), By Enterprise Size (Small & Medium Enterprises, Large Enterprises), By Application (Remote Access Security, Application Access Control, Secure Cloud Connectivity, Network Monitoring & Compliance, Others), By End Use (BFSI, IT and Telecommunications, Healthcare, Government & Defense, Retail & E-Commerce, Energy & Utilities, Education, Others), By Regional Analysis, Global Trends and Opportunity, Future Outlook By 2025-2035
- Published date: March 2026
- Report ID: 181513
- Number of Pages: 375
- Format:
-
keyboard_arrow_up
Quick Navigation
Report Overview
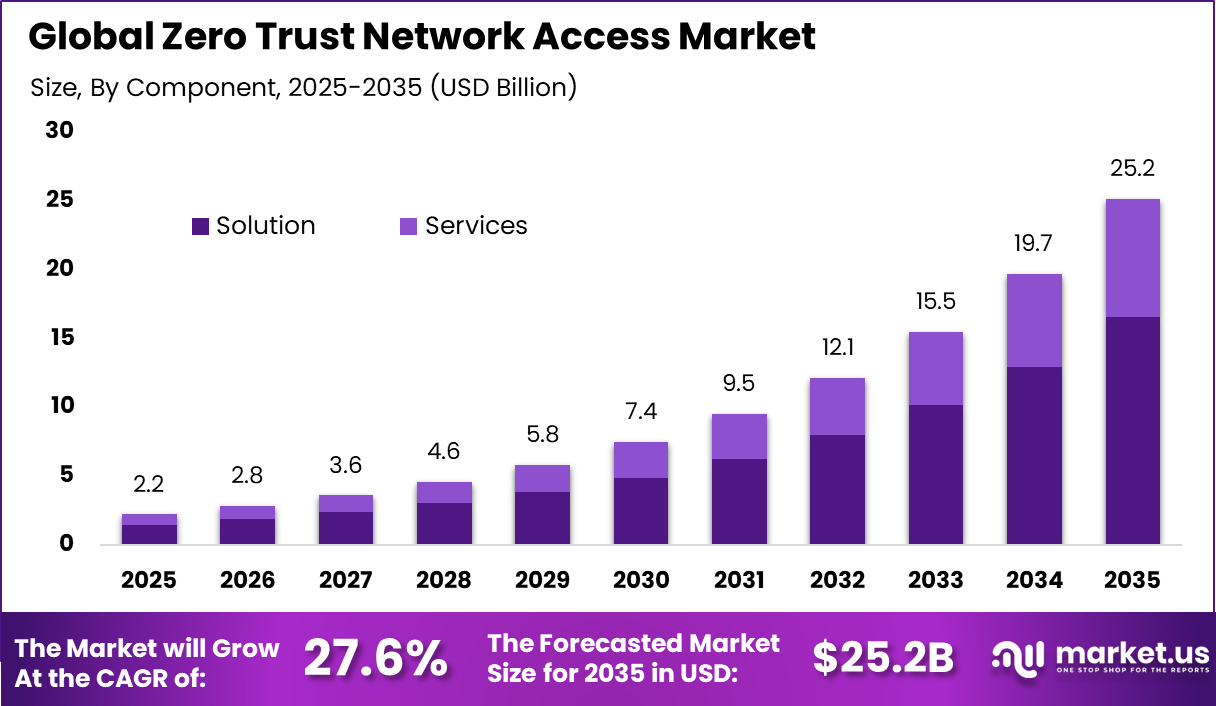
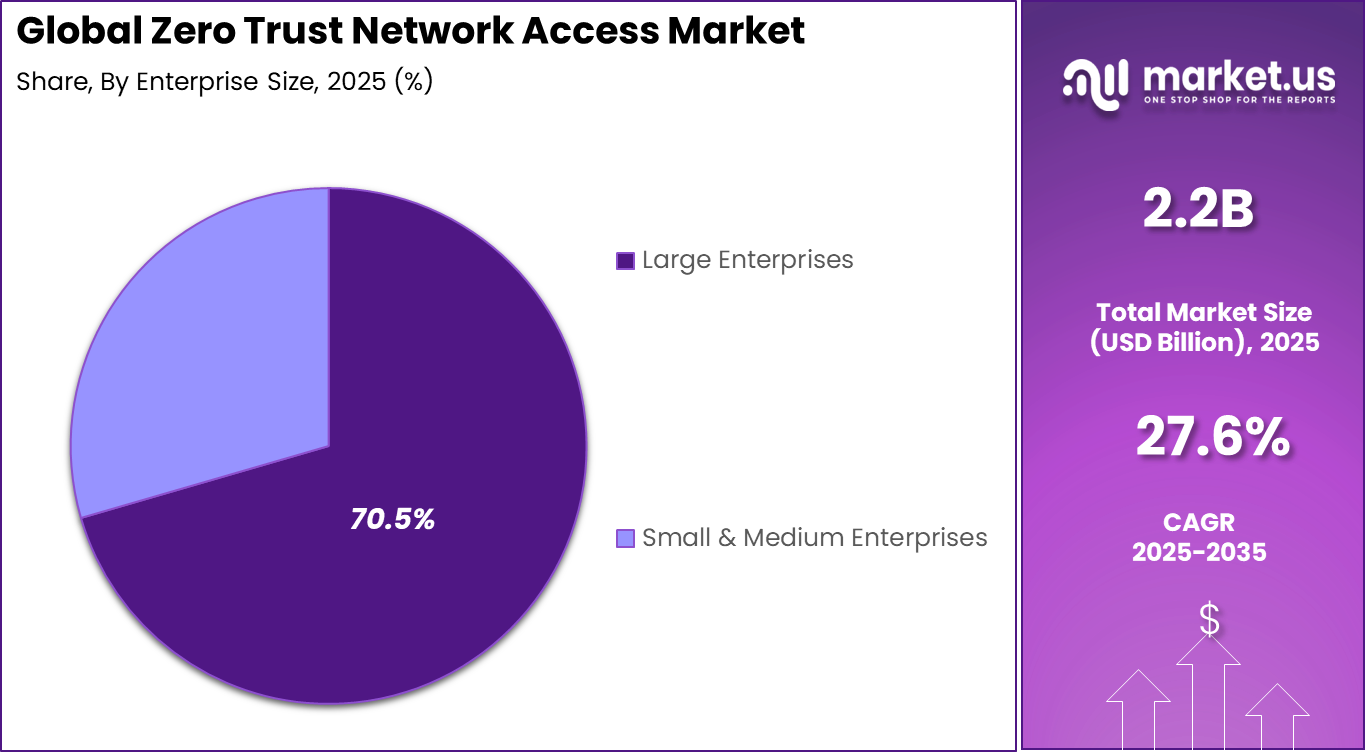
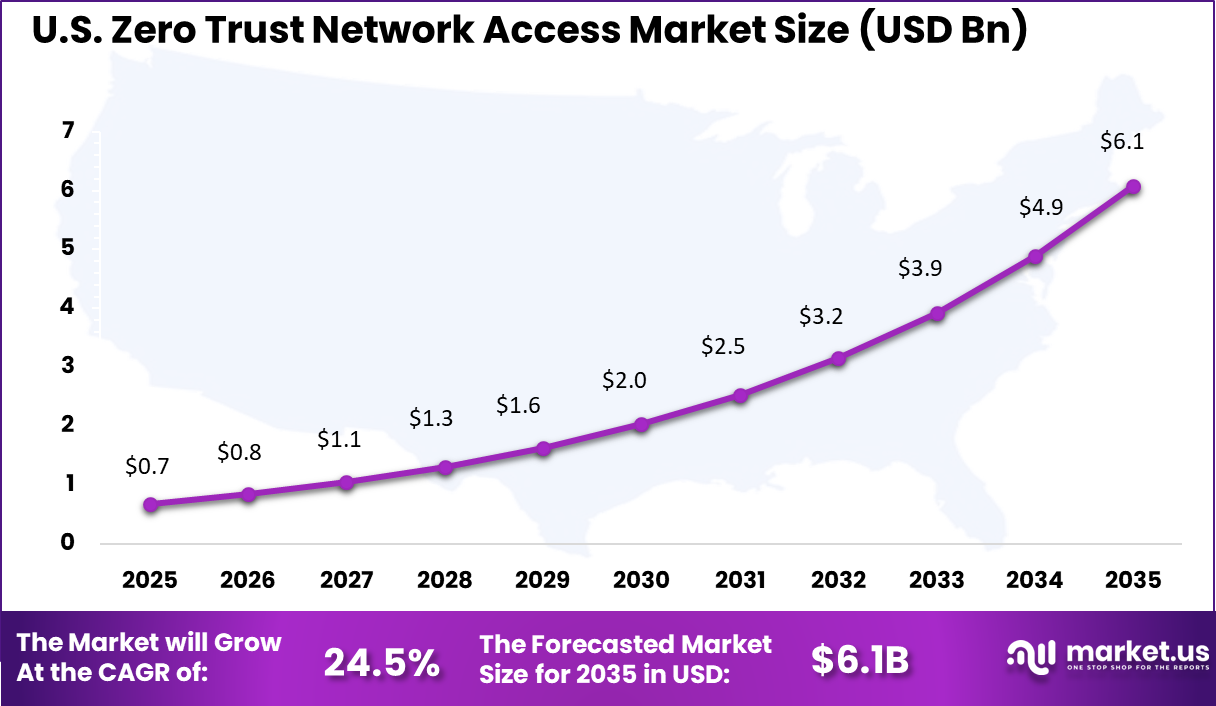
The Global Zero Trust Network Access Market size is expected to be worth around USD 25.2 Billion By 2035, from USD 2.2 billion in 2025, growing at a CAGR of 27.6% during the forecast period from 2026 to 2035. North America held a dominant Market position, capturing more than a 35.3% share, holding USD 0.7 Billion revenue.
The zero trust network access market focuses on security frameworks that enforce strict identity verification for every user and device attempting to access enterprise resources. Unlike traditional perimeter based models, zero trust operates on the principle that no entity is trusted by default and every access request must be continuously validated. This approach has gained strong traction as organizations adopt cloud infrastructure and remote work environments where network boundaries are no longer clearly defined.
The growth is driven by the increasing need to reduce attack surfaces and prevent unauthorized access. ZTNA limits access to only specific applications rather than exposing the entire network, which significantly reduces lateral movement during breaches. Enterprises are shifting from VPN based access models toward identity centric frameworks that provide granular control and continuous monitoring.
According to industry research, nearly 68% of enterprises are either using or actively adopting Zero Trust Network Access (ZTNA) to replace or complement traditional VPN solutions. This transition has been associated with measurable security improvements, including a reduction of approximately 58% in successful phishing incidents and nearly 45% lower lateral movement during security breaches, indicating stronger access control and threat containment capabilities.
Technological advancements in identity management, behavioral analytics, and device verification have strengthened the effectiveness of ZTNA solutions. Real time evaluation of user context, device posture, and access patterns enables dynamic access decisions. As cyber threats become more advanced, zero trust network access is increasingly viewed as a foundational element of enterprise cybersecurity strategies.
Top Market Takeaways
- In 2025, the Solution segment led the Zero Trust Network Access Market, accounting for 65.7% of total share.
- In 2025, On Premise deployment remained dominant, capturing 60.3% of the market.
- In 2025, Large Enterprises represented the primary customer segment with a 70.5% share.
- In 2025, Remote Access Security emerged as the leading application area, contributing 37.8% of overall demand.
- In 2025, the BFSI sector held the largest end use share at 38.8%.
- In 2025, North America secured a 35.3% regional share, while the U.S. market reached USD 0.68 billion and recorded a strong growth rate of 24.5%.
Key Insights Summary
- Full implementation of a Zero Trust framework can prevent up to 78% of potential security breaches.
- Around 87% of organizations report a significant decline in overall security incidents after adopting ZTNA.
- Organizations using ZTNA experience 47% fewer successful phishing attacks, 62% fewer ransomware incidents, and a 55% reduction in insider threats.
- Threat detection and response times improve by up to 50% following deployment.
- Approximately 52% of organizations have completed full ZTNA deployment, while 38% remain in partial implementation phases.
- About 35% of enterprises identify legacy infrastructure complexity as a key deployment barrier.
- Nearly 54% of IT leaders cite budget limitations as a constraint, and 35% report insufficient in house expertise for maintenance.
- Around 68% of enterprises deploy ZTNA to replace or supplement traditional VPN solutions.
- By the end of 2025, 95% of U.S. federal agencies are expected to align with Zero Trust compliance mandates.
By Component
Solutions account for 65.7% of the market, reflecting the growing demand for integrated platforms that manage identity verification, access control, and network security. These solutions continuously monitor user activity and enforce strict authentication protocols before granting access to enterprise resources. Organizations use these platforms to reduce the risk of unauthorized access and data breaches.
The dominance of solution platforms is also supported by their ability to integrate with identity management systems and security monitoring tools. Automated policy enforcement and real time threat detection improve overall network security. As enterprises strengthen cybersecurity strategies, solution based zero trust platforms remain central to secure access management.
By Deployment
On premises deployment represents 60.3% of the market, indicating a strong preference for maintaining security infrastructure within internal environments. Many organizations handle sensitive data that requires strict governance and compliance controls. Internal deployment allows enterprises to maintain direct oversight of access management systems and enforce customized security policies.
Organizations operating in regulated industries often prefer on premises solutions to ensure compliance with data protection regulations. Integration with existing network infrastructure and legacy systems further supports this deployment model. As security concerns continue to grow, on premises deployment remains widely adopted.
By Enterprise Size
Large enterprises account for 70.5% of market adoption due to the complexity of their network environments and the scale of their digital operations. These organizations manage multiple users, devices, and applications across distributed networks. Zero trust network access platforms help centralize access control and ensure consistent security policies across the enterprise.
Large organizations also maintain dedicated cybersecurity teams responsible for monitoring and managing access to critical systems. Continuous authentication and verification processes help reduce the risk of insider threats and external attacks. As enterprise digital ecosystems expand, large enterprises remain the primary adopters of zero trust security solutions.
By Application
Remote access security represents 37.8% of the market application segment due to the growing need for secure connectivity in remote and hybrid work environments. Employees increasingly access corporate systems from various locations and devices, which increases security risks. Zero trust solutions ensure that access is granted only after continuous identity verification and device validation.
These platforms also monitor user behavior and detect anomalies that may indicate potential security threats. By implementing strict access controls, organizations can protect sensitive data while enabling remote work flexibility. As remote work models continue to evolve, remote access security remains a key application area.
By End Use
The BFSI sector accounts for 38.8% of market adoption due to the high sensitivity of financial data and strict regulatory requirements. Financial institutions rely on zero trust frameworks to secure access to banking systems, transaction platforms, and customer data. Continuous authentication and monitoring help prevent unauthorized access and fraud.
Financial organizations also face increasing cyber threats targeting digital banking services. Zero trust solutions provide enhanced visibility and control over network access, supporting compliance with regulatory standards. As digital financial services expand, the BFSI sector continues to invest in advanced access security technologies.
By Region
North America holds 35.3% of the market share due to strong adoption of advanced cybersecurity frameworks and digital infrastructure. Organizations across finance, healthcare, and technology sectors actively implement zero trust architectures to strengthen network security. The presence of mature enterprise IT ecosystems further supports regional growth.
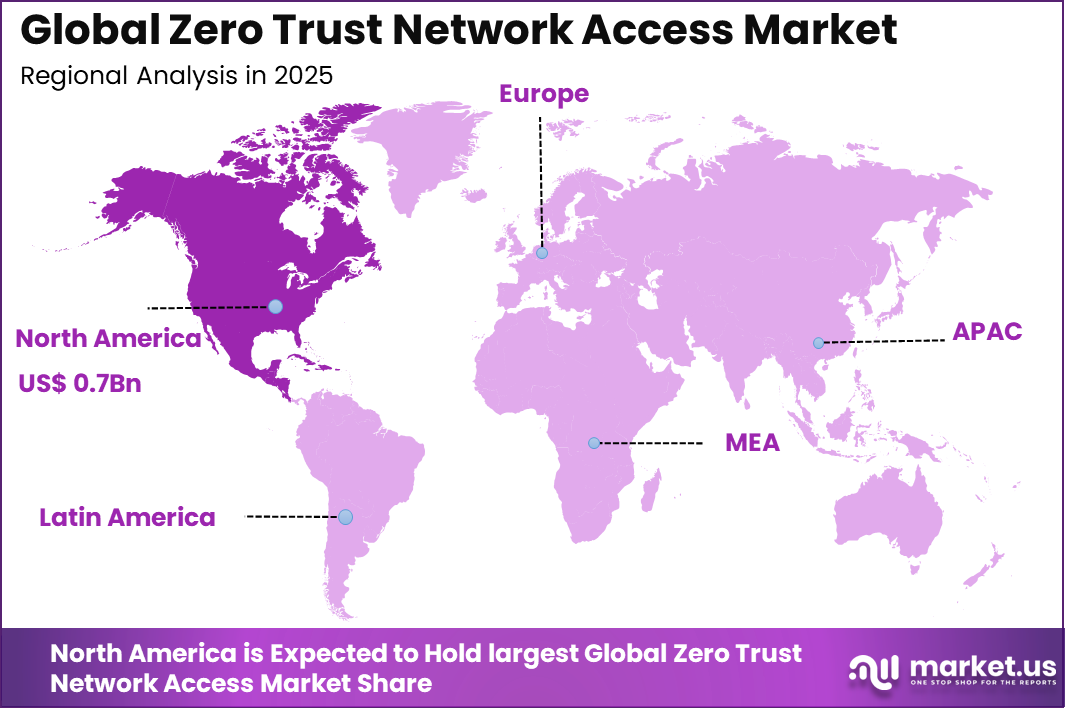
Within North America, the United States contributes USD 0.68 billion with a growth rate of 24.5%. The country’s large enterprise base and increasing cybersecurity threats have accelerated adoption of zero trust network access solutions. Continued investment in secure access technologies is expected to sustain market expansion across the region.
Growth Factors
One of the primary growth factors driving the ZTNA market is the widespread adoption of remote and hybrid work environments. Employees increasingly access enterprise systems from different locations and devices, which creates security challenges for traditional network models. ZTNA ensures secure, identity-based access regardless of user location, making it highly suitable for modern workforce structures.
Another growth factor is the rapid migration of enterprise applications to cloud and SaaS environments. As organizations move critical workloads outside traditional data centers, they require secure access frameworks that operate across distributed infrastructures. ZTNA solutions provide consistent security across cloud, on-premise, and hybrid environments, supporting this transition.
Emerging Trends
One emerging trend in the ZTNA market is the convergence with Secure Access Service Edge frameworks. Organizations are increasingly integrating ZTNA with broader cloud security architectures to create unified access and threat protection platforms. This integration enables centralized control over user access, network traffic, and security policies.
Another trend is the integration of artificial intelligence and behavioral analytics. AI-driven ZTNA platforms analyze user behavior, device posture, and contextual risk factors to dynamically adjust access permissions. This approach improves threat detection and ensures continuous verification throughout user sessions.
Key Market Segments
By Component
- Solution
- Services
By Deployment
- Cloud
- On-Premise
- Hybrid
By Enterprise Size
- Small & Medium Enterprises
- Large Enterprises
By Application
- Remote Access Security
- Application Access Control
- Secure Cloud Connectivity
- Network Monitoring & Compliance
- Others
By End Use
- BFSI
- IT and Telecommunications
- Healthcare
- Government & Defense
- Retail & E-Commerce
- Energy & Utilities
- Education
- Others
Regional Analysis and Coverage
- North America
- US
- Canada
- Europe
- Germany
- France
- The UK
- Spain
- Italy
- Russia
- Netherlands
- Rest of Europe
- Asia Pacific
- China
- Japan
- South Korea
- India
- Australia
- Singapore
- Thailand
- Vietnam
- Rest of Latin America
- Latin America
- Brazil
- Mexico
- Rest of Latin America
- Middle East & Africa
- South Africa
- Saudi Arabia
- UAE
- Rest of MEA
Driver
Rising Cybersecurity Threats
A key driver of the ZTNA market is the increasing frequency and sophistication of cyberattacks. Organizations face threats such as ransomware, phishing, and insider attacks, which exploit weaknesses in traditional network security models. ZTNA minimizes these risks by enforcing strict access controls and eliminating implicit trust within networks.
Another driver is the growing need for granular access control. Enterprises require solutions that allow them to define access policies based on user identity, device status, and context. ZTNA provides fine-grained access management, ensuring that users only access specific applications rather than entire networks.
Restraint
Deployment Complexity
One restraint affecting the ZTNA market is the complexity of implementation within existing IT environments. Organizations often operate legacy systems and traditional network architectures that require significant modification to support zero trust principles. Integrating ZTNA solutions with existing infrastructure can involve technical challenges and operational adjustments.
Another restraint is the need for continuous identity and access management. ZTNA relies heavily on accurate identity verification and policy enforcement, which requires robust identity management systems. Organizations without mature identity frameworks may face challenges in deploying ZTNA effectively.
Opportunity
Expansion of Zero Trust Architecture
A significant opportunity in the ZTNA market lies in the broader adoption of zero trust architecture across enterprises. As organizations move toward security models that eliminate implicit trust, ZTNA becomes a core component of these frameworks. This shift creates long-term demand for identity-based access solutions across industries.
Another opportunity involves expanding ZTNA applications beyond traditional IT environments into IoT, operational technology, and edge computing systems. As connected devices increase, organizations require secure access mechanisms that extend beyond conventional endpoints.
Challenge
Balancing Security and User Experience
One of the major challenges in the ZTNA market is maintaining a balance between strong security and user experience. Strict authentication and continuous verification processes may introduce latency or complexity for users. Organizations must design systems that provide robust security while ensuring seamless access for legitimate users.
Another challenge involves managing large volumes of access data. ZTNA systems generate continuous authentication and monitoring data, which must be analyzed in real time. Ensuring accurate threat detection without overwhelming security teams requires advanced analytics and automation capabilities.
Competitive Analysis
The Zero Trust Network Access Market is led by cybersecurity providers that deliver secure access solutions based on identity verification and continuous authentication. Zscaler, Inc., Palo Alto Networks, Cisco Systems, Inc., and Fortinet, Inc. provide platforms that replace traditional VPNs with cloud based secure access frameworks. These solutions enable organizations to control user access based on identity, device, and context.
Cloud security and identity management providers also play a significant role in this market. Cloudflare, Inc., Okta, Akamai Technologies, and Netskope deliver secure access service edge platforms that combine identity management with network security. These companies focus on protecting enterprise applications and data across distributed environments. Their solutions provide real time monitoring, threat detection, and secure connectivity across hybrid IT infrastructures.
Emerging vendors and specialized security providers further expand the competitive landscape. Appgate, Menlo Security, Nord Security, Twingate, and Zero Networks focus on identity based access control, micro segmentation, and secure application connectivity. Additional providers such as Omega Systems contribute managed security services and compliance solutions.
Top Key Players in the Market
- Akamai Technologies
- AppGate
- Check Point Software Technologies Ltd.
- Cisco Systems, Inc.
- Cloudflare, Inc.
- Fortinet, Inc.
- Menlo Security
- Netskope
- Nord Security
- Okta
- Omega Systems
- Palo Alto Networks
- Twingate
- Zero Networks
- Zscaler, Inc.
- Others
Recent Developments
- November, 2025 – Akamai launched Edge ZTNA with mTLS enforcement. Teams secure SaaS apps without agent installs. Global enterprises cut lateral movement risks by 60%. The platform proxies traffic through 250,000+ edge nodes. Device posture checks block 95% of risky endpoints. Akamai serves 4,000+ ZTNA customers.
- January, 2026 – Zscaler Private Access added browser isolation for legacy apps. Remote workers access RDP without VPN latency. Financial firms report 50% faster threat response. Workload segmentation covers Kubernetes clusters. Inline CASB prevents shadow IT. Zscaler processes 500 billion daily transactions.
Report Scope
Report Features Description Market Value (2025) USD 2.2 Bn Forecast Revenue (2035) USD 25.2 Bn CAGR (2026-2035) 27.6% Base Year for Estimation 2025 Historic Period 2020-2024 Forecast Period 2026-2035 Report Coverage Revenue forecast, AI impact on Market trends, Share Insights, Company ranking, competitive landscape, Recent Developments, Market Dynamics and Emerging Trends Segments Covered By Component (Solution, Services), By Deployment (Cloud, On-Premise, Hybrid), By Enterprise Size (Small & Medium Enterprises, Large Enterprises), By Application (Remote Access Security, Application Access Control, Secure Cloud Connectivity, Network Monitoring & Compliance, Others), By End Use (BFSI, IT and Telecommunications, Healthcare, Government & Defense, Retail & E-Commerce, Energy & Utilities, Education, Others) Regional Analysis North America – US, Canada; Europe – Germany, France, The UK, Spain, Italy, Russia, Netherlands, Rest of Europe; Asia Pacific – China, Japan, South Korea, India, New Zealand, Singapore, Thailand, Vietnam, Rest of Latin America; Latin America – Brazil, Mexico, Rest of Latin America; Middle East & Africa – South Africa, Saudi Arabia, UAE, Rest of MEA Competitive Landscape Akamai Technologies, AppGate, Check Point Software Technologies Ltd., Cisco Systems, Inc., Cloudflare, Inc., Fortinet, Inc., Menlo Security, Netskope, Nord Security, Okta, Omega Systems, Palo Alto Networks, Twingate, Zero Networks, Zscaler, Inc., Others Customization Scope Customization for segments, region/country-level will be provided. Moreover, additional customization can be done based on the requirements. Purchase Options We have three license to opt for: Single User License, Multi-User License (Up to 5 Users), Corporate Use License (Unlimited User and Printable PDF)  Zero Trust Network Access MarketPublished date: March 2026add_shopping_cartBuy Now get_appDownload Sample
Zero Trust Network Access MarketPublished date: March 2026add_shopping_cartBuy Now get_appDownload Sample -
-
- Akamai Technologies
- AppGate
- Check Point Software Technologies Ltd.
- Cisco Systems, Inc.
- Cloudflare, Inc.
- Fortinet, Inc.
- Menlo Security
- Netskope
- Nord Security
- Okta
- Omega Systems
- Palo Alto Networks
- Twingate
- Zero Networks
- Zscaler, Inc.
- Others